Cybersecurity services
Security Consulting
Our expert cybersecurity services engineers and consultants provide strategic guidance to fortify your digital defenses across your entire infrastructure. We work closely with your organization to identify vulnerabilities, assess risks, and develop comprehensive security roadmaps. This includes defining and implementing critical security requirements such as enterprise cloud security and cybersecurity consulting, penetration testing, Azure Sentinel, hybrid multicloud security, and dark web monitoring.
Network Security
Implementing firewalls, intrusion detection/prevention systems (IDS/IPS), and secure network segmentation to protect against unauthorized access and cyber threats.
Endpoint Security
Deploying advanced endpoint detection and response (EDR) solutions, antivirus, and anti-malmalware to secure all devices connected to your network
Data Security
Establishing robust encryption protocols for data at rest and in transit, implementing data loss prevention (DLP) strategies, and ensuring proper data classification and access controls.
Application Security
Integrating security best practices into the software development lifecycle (SDLC), conducting regular vulnerability assessments and penetration testing for applications, and securing APIs.
Identity and Access Management (IAM)
Implementing strong authentication mechanisms like multi-factor authentication (MFA), role-based access control (RBAC), and privileged access management (PAM) to control who has access to what resources.
Cloud Security
Ensuring secure configurations for cloud environments, managing cloud identity and access, and continuously monitoring cloud resources for misconfigurations and threats.
Compliance and Governance
Assisting with adherence to industry regulations (e.g., GDPR, HIPAA, ISO 27001) and developing security policies and procedures. Our goal is to build a resilient security posture that protects your assets, maintains compliance, and enables secure business operations.
Cybersecurity Assessment
Our cybersecurity assessments provide a comprehensive evaluation of your organization’s security posture to identify vulnerabilities, weaknesses, and potential risks across your IT infrastructure. We utilize a range of assessment strategies to gain a holistic view of your security landscape:
Vulnerability Assessments
Automated and manual scans to identify known security weaknesses in systems, applications, and networks. This includes identifying missing patches, misconfigurations, and other common vulnerabilities.
Penetration Testing (Pen Testing)
Simulating real-world cyberattacks to uncover exploitable vulnerabilities and assess the effectiveness of existing security controls. This can include external (internet-facing), internal (within the network), web application, and mobile application penetration tests.
Security Audits
A systematic review of your security policies, procedures, and controls against established standards (e.g., ISO 27001, NIST, PCI DSS) and regulatory requirements. This helps ensure compliance and identifies gaps in your security framework.
Risk Assessments
Identifying, analyzing, and evaluating potential risks to your information assets. This involves understanding the likelihood of threats exploiting vulnerabilities and the potential impact on your business, leading to prioritized mitigation strategies.
Social Engineering Assessments
Testing the human element of your security by simulating phishing attacks, pretexting, or other social engineering tactics to gauge employee awareness and susceptibility. These assessments provide actionable insights and a clear roadmap for strengthening your defenses and reducing your attack surface.
Security Architecture Review
An in-depth examination of your current security architecture, including network design, cloud configurations, and system integrations, to identify design flaws and areas for improvement.
Audit and Reporting
We provide detailed insights into your security compliance and performance through comprehensive audit and reporting services. Our rigorous audits go beyond simple checks, offering a clear picture of your organization’s security landscape. This adds significant value to your IT operations by:
Ensuring Regulatory Compliance
We help you navigate complex regulatory landscapes (e.g., GDPR, HIPAA, PCI DSS, SOX, ISO 27001) by verifying that your IT systems and processes adhere to the necessary standards. Our reports provide the documentation required for regulatory reviews, helping you avoid costly fines and reputational damage
Facilitating Informed Decision-Making
Our detailed reports provide management and stakeholders with a clear understanding of your current security status, identified risks, and the effectiveness of your security investments. This data-driven approach enables better strategic planning and resource prioritization for cybersecurity initiatives.
Improving Security Posture
By systematically reviewing your security controls, policies, and procedures, we identify gaps and weaknesses that could be exploited by cyber threats. Our reports offer actionable recommendations for remediation, allowing you to proactively strengthen your defenses and reduce your overall risk exposure.
Building Trust and Credibility
Demonstrating a commitment to robust security through regular audits and transparent reporting enhances trust with customers, partners, and investors, reinforcing your organization's reputation as a secure and reliable entity.
Enhancing Operational Efficiency
Audits can uncover inefficiencies in security processes or redundant systems, leading to recommendations that streamline operations and optimize resource allocation. This can result in cost savings and improved productivity.
Supporting Continuous Improvement
Audit and reporting are not one-time events but part of an ongoing feedback loop. Our services help you establish a continuous monitoring and improvement process, ensuring your security measures evolve with the threat landscape and business changes.
Azure Sentinel Consulting
We offer specialized expertise in leveraging Azure Sentinel for advanced threat detection and as a powerful, cloud-native Security Operations Center (SOC) solution. Our consultants help you maximize Sentinel’s capabilities to:
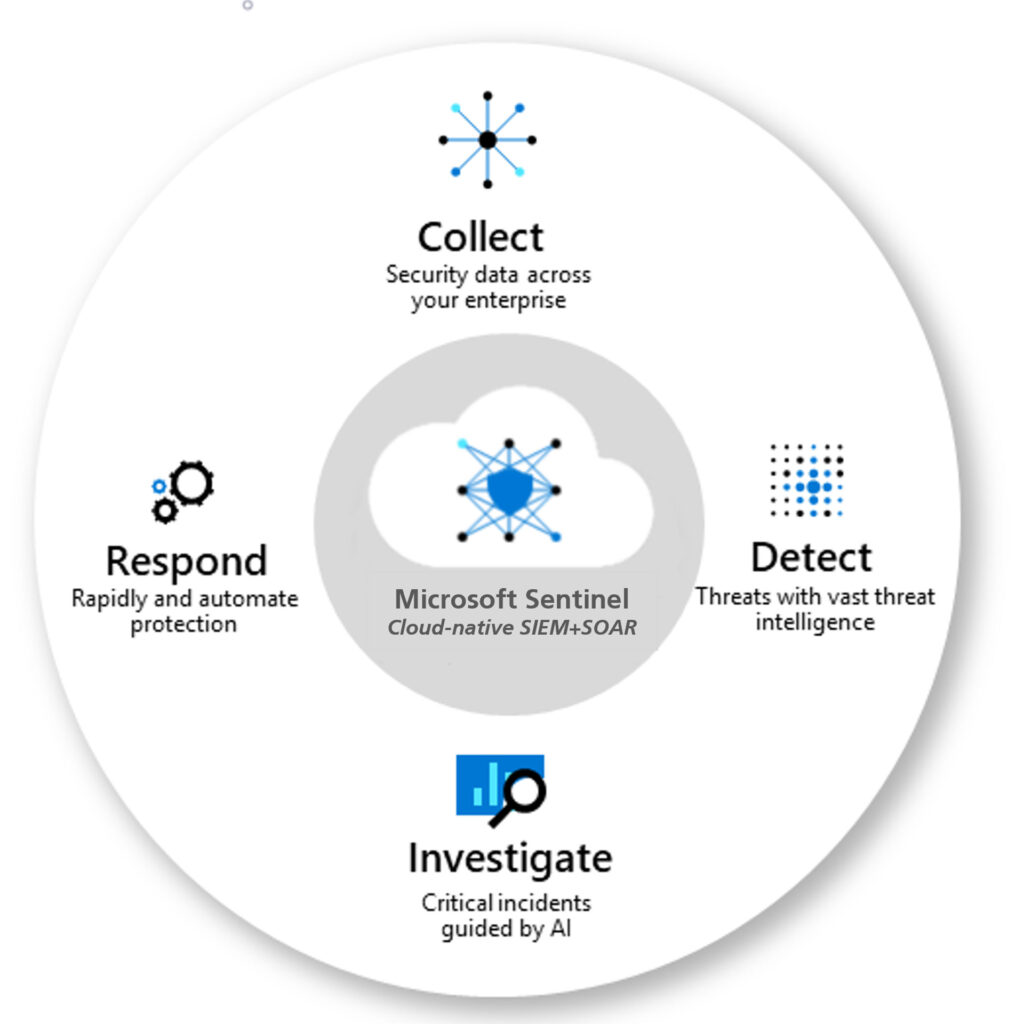
Centralized Log Ingestion
Collect security data at cloud scale from all your sources, including Microsoft 365, Azure services, on-premises infrastructure, and third-party security solutions, providing a unified view of your security landscape.
Integrated Threat Intelligence
Integrate various threat intelligence feeds (Microsoft's own and third-party) to enrich alerts and provide crucial context for faster and more informed investigation and response decisions.
Proactive Threat Hunting
Empower your security analysts with advanced hunting capabilities using Kusto Query Language (KQL) to proactively search for hidden threats and uncover attack patterns before they escalate into major incidents.
Automated Incident Response (SOAR)
Implement Security Orchestration, Automation, and Response (SOAR) playbooks to automate routine security tasks, such as incident enrichment, containment, and remediation, drastically reducing Mean Time To Respond (MTTR) to threats.
Compliance and Reporting
Leverage Sentinel's robust reporting and dashboarding features to monitor your security posture, track key performance indicators, and demonstrate compliance with regulatory requirements. Our consulting ensures that Azure Sentinel is optimally configured and utilized to provide comprehensive threat visibility, rapid incident response, and a highly efficient SOC operation tailored to your organization's unique needs.
AI-Powered Threat Detection
Utilize Azure Sentinel's built-in AI and machine learning to detect subtle anomalies and sophisticated threats that might otherwise go unnoticed, significantly reducing false positives and alert fatigue. This includes User and Entity Behavior Analytics (UEBA) to identify suspicious user activities.
Hybrid Multicloud Security
We specialize in securing your diverse IT environments that span across private clouds, Azure, and AWS, often integrating with other on-premises infrastructure. This comprehensive approach addresses the inherent complexities of hybrid and multicloud environments, such as inconsistent security policies, fragmented visibility, and varying compliance requirements across these distinct providers. Our strategy focuses on:

Unified Security Posture
Implementing consistent security policies and controls across all your private cloud, Azure, AWS, and other on-premises environments. This includes harmonizing Identity and Access Management (IAM) across platforms (e.g., your private cloud's IAM, Azure Active Directory, and AWS IAM), ensuring least privilege access, and centralizing authentication to provide a seamless yet secure user experience.
Centralized Visibility and Monitoring
Aggregating security logs and events from your private cloud infrastructure, Azure (e.g., Azure Monitor, Azure Security Center), and AWS (e.g., AWS CloudWatch, AWS Security Hub) into a unified Security Information and Event Management (SIEM) solution, such as Azure Sentinel. This provides a single pane of glass for comprehensive threat detection, incident response, and real-time insights across your entire hybrid multicloud footprint.
Data Protection Across All Environments
Ensuring robust encryption for data at rest and in transit across private clouds, Azure, and AWS using native cloud services (e.g., Azure Key Vault, AWS KMS, and your private cloud's encryption solutions). We also implement consistent data loss prevention (DLP) strategies and data classification policies to protect sensitive information wherever it resides.
Integrated Network Security
Designing secure network architectures that seamlessly connect your on-premises data centers and private clouds with Azure Virtual Networks (VNets) and AWS Virtual Private Clouds (VPCs). This involves utilizing advanced firewalls, network security groups, intrusion detection/prevention systems, and secure VPN/Direct Connect solutions for resilient and secure communication pathways between all environments.
Compliance Across Jurisdictions and Platforms
Navigating and ensuring adherence to various industry regulations and data residency requirements that may differ across private cloud deployments, public cloud providers (Azure, AWS), and geographical locations. We help establish governance frameworks that ensure continuous compliance. Our expertise ensures that your hybrid multicloud environment, encompassing private clouds, Azure, and AWS, is not only secure but also optimized for performance and compliance, allowing you to leverage the best of each platform without compromising your security posture.
Automated Security Operations
Leveraging automation tools and Infrastructure as Code (IaC) (e.g., Ansible, Terraform) to ensure consistent security configurations, rapid deployment of security controls, and automated responses to detected threats across your private cloud, Azure, and AWS environments. This minimizes manual errors and accelerates remediation.
Public Cloud Security Solutions
We provide tailored security measures specifically designed for your public cloud deployments, leveraging the native security capabilities of leading providers like Azure and AWS. Our approach ensures your public cloud infrastructure, applications, and data are protected against evolving threats and remain compliant with industry standards. Key aspects of our public cloud security solutions include:
Our tailored public cloud security solutions ensure that your deployments on Azure and AWS are not only highly secure but also optimized for performance, cost, and compliance, allowing you to fully leverage the agility and scalability of the public cloud.
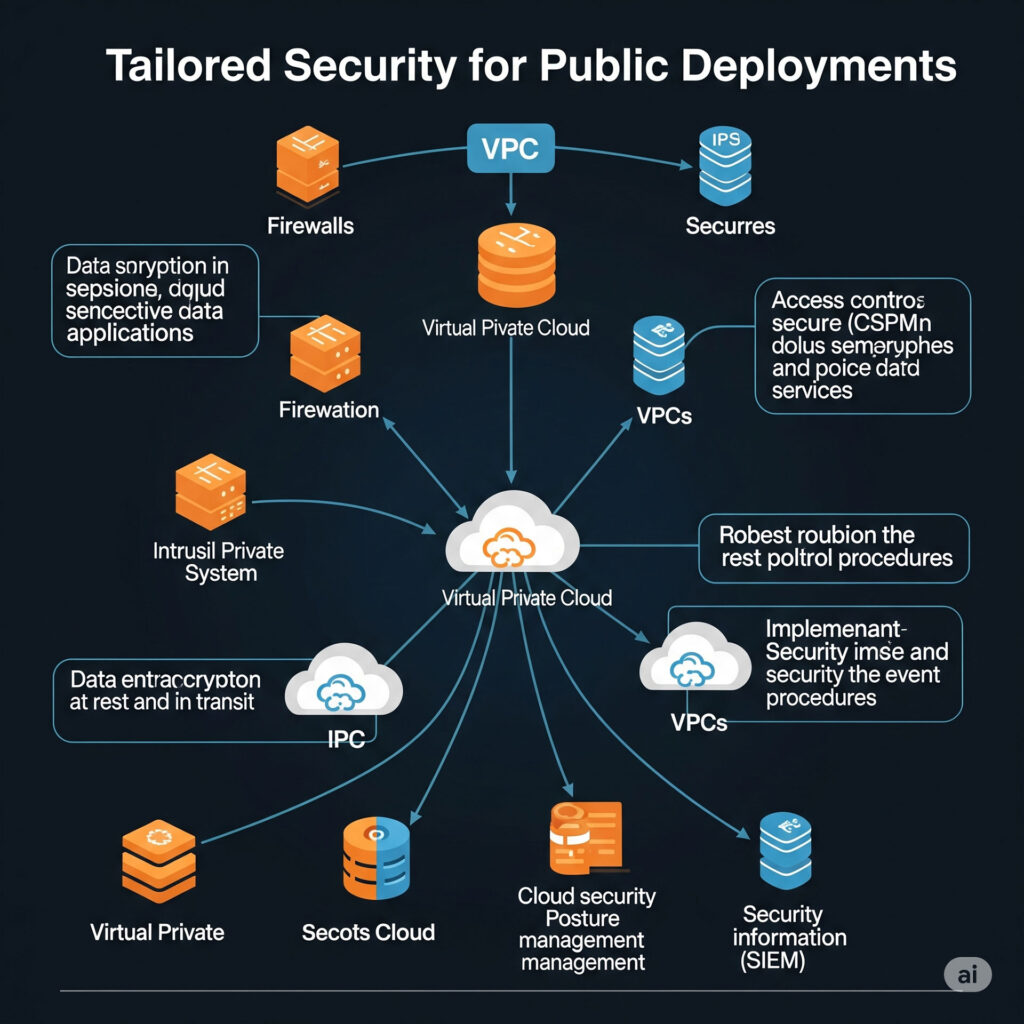
Identity and Access Management (IAM)
Azure
We implement robust IAM using Azure Active Directory (Azure AD), focusing on Multi-Factor Authentication (MFA), Conditional Access policies, Role-Based Access Control (RBAC), and Privileged Identity Management (PIM) to ensure least privilege and secure access to Azure resources.
AWS
We configure AWS Identity and Access Management (IAM), setting up granular permissions with roles and policies, enforcing MFA for all users, and utilizing services like AWS SSO and Amazon Cognito for centralized identity management and secure application access.
Security Monitoring and Compliance
Azure
We leverage Microsoft Defender for Cloud for continuous security posture management and threat protection, and Azure Monitor for logging and analytics. We also assist with achieving and maintaining compliance with standards like ISO 27001, HIPAA, and GDPR through Azure Policy and Compliance Manager.
AWS
We utilize AWS Security Hub for centralized security findings, Amazon GuardDuty for intelligent threat detection, and AWS CloudTrail for auditing API activity. We also ensure compliance with standards like PCI DSS and ISO 27001, providing automated compliance checks through AWS Config and AWS Audit Manager.
Data Protection
Azure
We ensure data confidentiality and integrity using Azure Storage Service Encryption (SSE) for data at rest, Azure Key Vault for secure key management, and TLS/SSL for data in transit. We also implement Data Loss Prevention (DLP) strategies.
AWS
We protect your data with Amazon S3 encryption for data at rest, AWS Key Management Service (KMS) for cryptographic key management, and TLS for secure data transfer. We also leverage Amazon Macie for sensitive data discovery and protection.
Network Security
Azure
We secure your Azure networks with Azure Firewall, Network Security Groups (NSGs), Azure DDoS Protection, and Web Application Firewall (WAF) to control traffic, prevent unauthorized access, and mitigate denial-of-service attacks.
AWS
We deploy AWS Virtual Private Cloud (VPC) with security groups and network ACLs, utilize AWS WAF and AWS Shield for application and DDoS protection, and implement AWS Network Firewall for centralized traffic filtering.
Dark Web Monitoring
Our Dark Web Monitoring service provides proactive surveillance of the hidden parts of the internet to detect compromised credentials and sensitive data belonging to your organization. The dark web is a clandestine network where cybercriminals anonymously trade stolen information, making it a critical source of early warning for potential security breaches.
By continuously monitoring the dark web, we provide an essential layer of defense, transforming a potential blind spot into a source of actionable intelligence to secure your digital assets.

Detection of Compromised Credentials
A primary focus is identifying leaked login credentials (usernames, passwords, security question answers) that cybercriminals often steal through phishing attacks, malware, or data breaches. When a match is found, our system flags it immediately.
Threat Intelligence and Analysis
The raw intelligence collected from the dark web is analyzed to provide valuable insights into evolving threat actor tactics, techniques, and procedures (TTPs). This helps in understanding emerging cyber threats, potential attack vectors, and the methods criminals might use to exploit vulnerabilities.
Real-time Alerts and Reporting
Upon detection of compromised data or relevant threat intelligence, our service generates real-time alerts, notifying your security team. We provide detailed reports outlining the type of information compromised, its potential impact, and actionable recommendations for remediation. This allows for swift action, such as resetting passwords, revoking access, or initiating incident response procedures, to minimize damage.
Continuous Scanning and Data Collection
We employ specialized tools and techniques to continuously scan various dark web sources, including illicit marketplaces, underground forums, paste sites, and encrypted chat rooms. Our crawlers are programmed to search for specific keywords, corporate email addresses, domain names, intellectual property, financial information (e.g., credit card numbers, bank accounts), personally identifiable information (PII), and other sensitive data associated with your business or employees.
Value to Your Business
Proactive Risk Mitigation
Allows you to address potential vulnerabilities before they are exploited, preventing costly cyberattacks.
Early Breach Detection
Significantly reduces the time to detect a data breach, enabling faster response and mitigation.
Protection of Sensitive Assets
Safeguards critical business data, intellectual property, and customer information from unauthorized access and sale.
Enhanced Incident Response
Provides crucial intelligence that streamlines investigation and accelerates recovery efforts.
Brand Reputation Management
Protects your company's reputation and maintains customer trust by demonstrating a proactive stance on cybersecurity.
Compliance Support
Helps meet regulatory requirements for data protection and breach notification by providing timely insights into data exposure.
