Cloud Services
Cloud Consulting Services
We provide strategic advice and planning for your cloud adoption and optimization. Our comprehensive consulting services guide your organization through every stage of its cloud journey, ensuring a successful and impactful transition. This includes:
Cloud Readiness Assessment
Evaluating your current IT infrastructure, applications, and business processes to determine your readiness for cloud adoption. This involves identifying suitable workloads for migration, assessing technical complexities, and understanding organizational capabilities.
Cloud Strategy Development
Crafting a tailored cloud strategy that aligns with your business objectives. This includes defining cloud models (public, private, hybrid, multi-cloud), selecting appropriate cloud providers (e.g., Azure, AWS, Google Cloud), and outlining a clear roadmap for implementation.
Cloud Migration Planning & Execution
Developing detailed migration plans for applications and data, choosing the right migration strategies (rehost, refactor, re-platform, repurchase, retire, retain), and executing the migration with minimal disruption to operations.
Cloud Architecture Design
Designing scalable, resilient, and secure cloud architectures that leverage cloud-native services and best practices. This ensures your cloud environment is optimized for performance, cost-efficiency, and future growth.
Cloud Cost Optimization (FinOps)
Implementing strategies and tools to manage and optimize your cloud spending. This includes cost visibility, resource right-sizing, reserved instances/savings plans utilization, and automated cost governance to maximize your cloud ROI.
Cloud Governance & Compliance
Establishing robust governance frameworks and policies to ensure compliance with industry regulations (e.g., GDPR, HIPAA, PCI DSS) and internal security standards within your cloud environment.
Cloud Native Development & Modernization
Guiding the adoption of cloud-native development practices (e.g., microservices, containers, serverless computing) and modernizing existing applications to fully leverage the benefits of the cloud.
Cloud Security Integration
Integrating comprehensive security measures into your cloud environment from the ground up, covering identity, network, data, and application security, as well as continuous monitoring and threat detection. Our goal is to ensure your cloud adoption is not just a technological shift, but a strategic move that drives innovation, agility, and competitive advantage for your business.
Identity and Access Management (IAM)
We provide comprehensive solutions for securely managing user identities and access privileges across your entire IT ecosystem. Identity and Access Management is a critical security discipline that ensures only authorized individuals and systems can access specific resources, at the right time, and for the right reasons. Our services in this area include:
Behavioral Anomaly Detection
Utilizing advanced analytics and machine learning to identify deviations from normal user and system behavior, which can indicate compromised accounts, insider threats, or novel attack techniques.
Authentication Management
Deploying strong authentication mechanisms to verify user identities. This includes:
Multi-Factor Authentication (MFA)
Requiring users to provide two or more verification factors (e.g., password + mobile app code, biometric scan) to significantly enhance security and prevent unauthorized access even if passwords are compromised.
Single Sign-On (SSO)
Enabling users to access multiple applications and services with a single set of credentials, improving user experience while maintaining robust security.
Authorization and Access Control
Defining and enforcing granular access policies to control what users can do once authenticated. This involves:
Role-Based Access Control (RBAC)
Assigning permissions based on job roles and responsibilities, ensuring users only have access to the resources necessary for their functions.
Attribute-Based Access Control (ABAC)
Implementing more dynamic access policies based on various attributes (user attributes, resource attributes, environmental conditions).
Least Privilege Principle
Ensuring users and systems are granted only the minimum necessary permissions to perform their tasks, reducing the attack surface.
Privileged Access Management (PAM)
Securing, managing, and monitoring privileged accounts (e.g., administrator accounts, service accounts) that have elevated access to critical systems and sensitive data. This includes just-in-time (JIT) access, session recording, and credential vaulting.
API Security & Identity for Applications
Securing API access and managing identities for applications and microservices, ensuring secure communication and authorized access to data. By implementing robust IAM strategies, we help your organization reduce the risk of unauthorized access, enhance data protection, streamline compliance, and improve overall operational efficiency.
Identity Governance and Administration (IGA)
Establishing processes for managing the entire identity lifecycle, including user provisioning/de-provisioning, access request workflows, regular access reviews, and segregation of duties to ensure compliance and prevent "privilege creep."
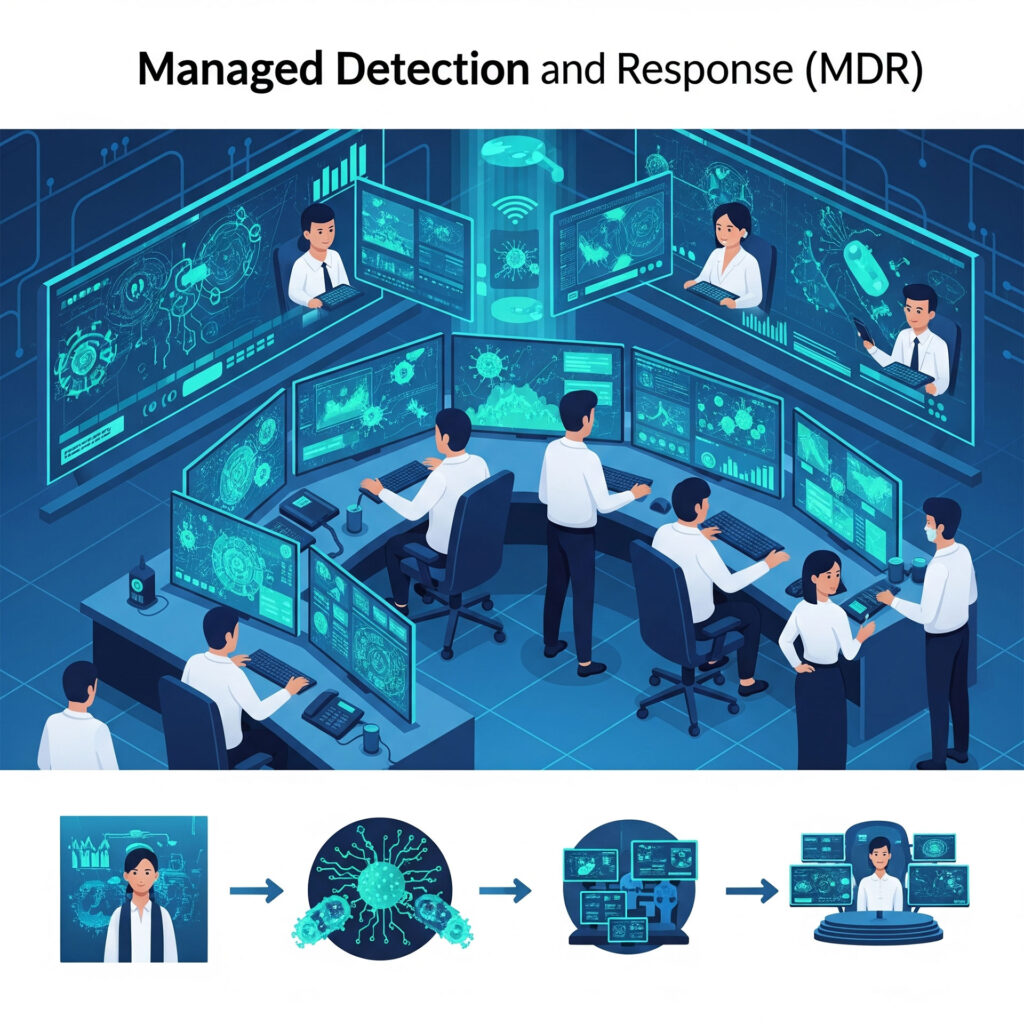
Threat Detection and Response
Our Threat Detection and Response service focuses on the proactive identification of potential cyber threats and the swift, effective actions required to neutralize them. In today’s dynamic threat landscape, simply reacting to attacks is insufficient. Our comprehensive approach ensures your organization is prepared to anticipate, detect, and respond to security incidents with speed and precision. This includes:
Our Threat Detection and Response service provides a robust, layered defense that enables your organization to stay ahead of cyber adversaries, minimize the impact of security incidents, and maintain a resilient security posture.
Continuous Monitoring
Implementing 24/7 monitoring of your IT infrastructure, networks, endpoints, and cloud environments to collect security logs, events, and telemetry data. This continuous vigilance allows us to spot anomalous behavior and indicators of compromise (IoCs) in real-time.
Behavioral Analytics (UEBA)
Utilizing User and Entity Behavior Analytics (UEBA) to establish baselines of normal activity for users, devices, and applications. This allows us to detect deviations from these baselines, indicating potential insider threats, compromised accounts, or advanced persistent threats (APTs) that might bypass traditional signature-based defenses.
Advanced Threat Intelligence Integration
Leveraging up-to-date threat intelligence feeds from various sources (e.g., industry-specific intelligence, dark web monitoring, global threat landscape data) to enrich detected events, understand attacker methodologies (TTPs), and identify emerging threats relevant to your organization.
Automated Detection and Alerting
Employing Security Information and Event Management (SIEM) and Extended Detection and Response (XDR) platforms to correlate events from disparate sources, apply machine learning algorithms, and generate high-fidelity alerts for genuine threats while minimizing false positives.
Proactive Threat Hunting
Our expert security analysts actively search for hidden threats within your environment that automated tools might miss. This involves developing custom queries, analyzing raw data, and following leads based on threat intelligence to uncover sophisticated attacks before they cause significant damage.
Rapid Incident Response Planning and Execution
Developing and regularly testing comprehensive incident response plans tailored to your organization’s specific risks. In the event of a confirmed incident, we execute these plans swiftly to:
Containment
Isolate affected systems to prevent further spread of the attack
Eradication
Remove the threat from your environment.
Recovery
Restore affected systems and data to normal operations
Post-Incident Analysis
Conduct a thorough review to identify root causes, lessons learned, and implement measures to prevent recurrence.
Security Orchestration, Automation, and Response (SOAR):
Implementing SOAR playbooks to automate repetitive security tasks, such as alert triage, data enrichment, and initial response actions (e.g., blocking malicious IPs, isolating endpoints). This significantly reduces Mean Time To Detect (MTTD) and Mean Time To Respond (MTTR).
Our Threat Detection and Response service provides a robust, layered defense that enables your organization to stay ahead of cyber adversaries, minimize the impact of security incidents, and maintain a resilient security posture.
Compliance Management
Our Compliance Management service ensures your organization’s adherence to industry regulations, legal requirements, and internal standards within your cloud environments. Navigating the complex landscape of compliance is crucial for avoiding penalties, maintaining trust, and demonstrating a strong security posture. Our services include:

Regulatory Mapping and Gap Analysis
Identifying all relevant industry regulations (e.g., GDPR, HIPAA, PCI DSS, ISO 27001, SOC 2, NIST) applicable to your cloud operations. We then perform a detailed gap analysis to assess your current compliance posture against these requirements.
Policy Development and Implementation
Assisting in the development and implementation of robust security policies, procedures, and controls that meet specific compliance mandates. This includes data governance, access control policies, incident response procedures, and audit trails.
Continuous Compliance Monitoring
Implementing automated tools and processes to continuously monitor your cloud resources and configurations for compliance deviations. This proactive approach helps identify and remediate non-compliant settings in real-time.
Audit Preparation and Support
Guiding your organization through internal and external audits. We help prepare necessary documentation, provide evidence of controls, and support your teams throughout the audit process to ensure successful outcomes.
Risk Assessment and Mitigation
Integrating compliance requirements into your overall risk management framework. We help assess the risks associated with non-compliance and develop strategies to mitigate them effectively.
Data Residency and Sovereignty
Addressing specific requirements related to where data is stored and processed, especially for global operations, to ensure adherence to local data protection laws.
Reporting and Documentation
Generating comprehensive compliance reports and maintaining detailed documentation of your compliance status, controls, and audit trails, which are essential for demonstrating due diligence to auditors and stakeholders. Our Compliance Management service provides the expertise and tools necessary to build and maintain a strong compliance framework in the cloud, reducing your risk exposure and fostering stakeholder confidence.
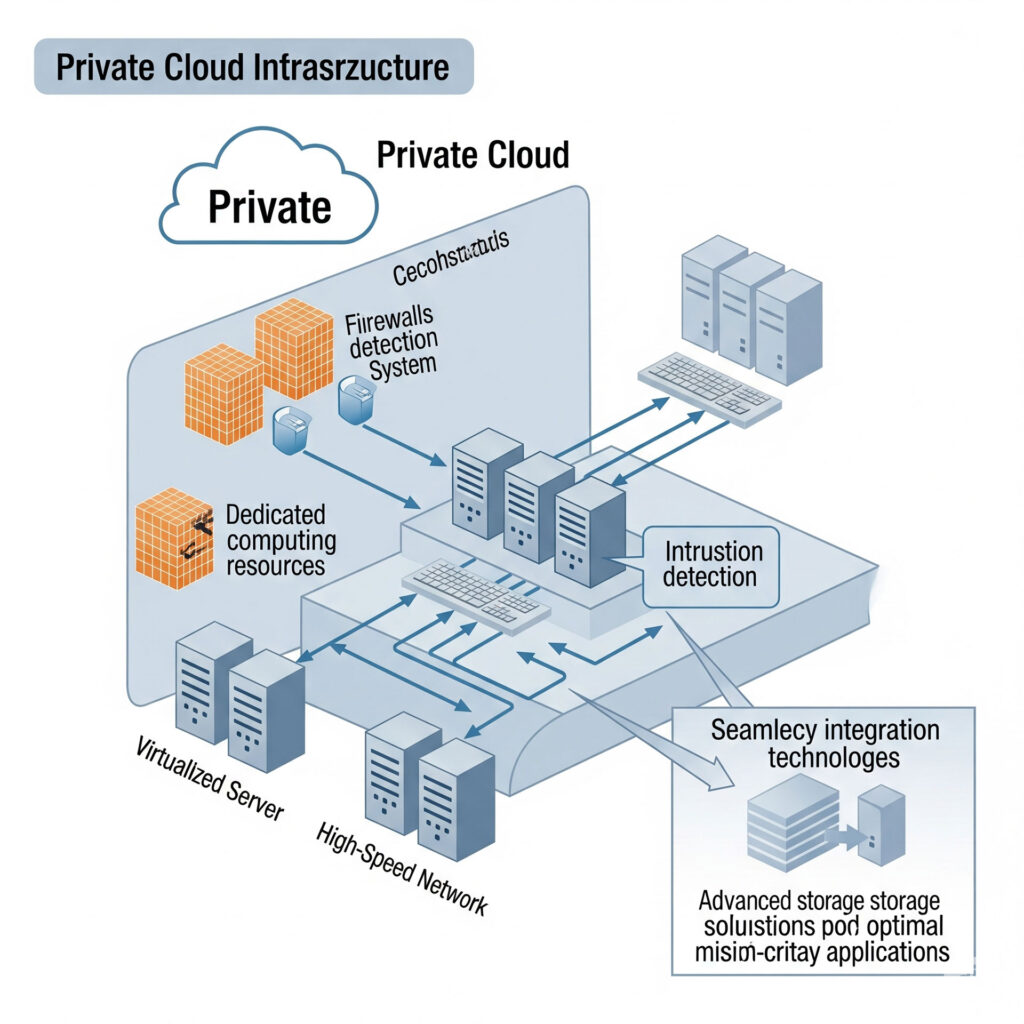
Private Cloud Setup
We specialize in designing and implementing secure and scalable private cloud infrastructures tailored to your organization’s unique needs. A private cloud provides dedicated computing resources, offering enhanced control, security, and performance compared to public cloud environments. Our comprehensive approach covers:
Needs Assessment and Planning
Collaborating with your team to understand your business objectives, workload requirements, security mandates, and compliance needs. This forms the foundation for a customized private cloud design.
Architecture Design
Developing a robust and resilient private cloud architecture, including compute, storage, networking, and virtualization layers. We focus on high availability, fault tolerance, and performance optimization.
Platform Selection and Implementation
Guiding you in selecting the most suitable private cloud platform (e.g., VMware vSphere, OpenStack, Microsoft Azure Stack HCI, Nutanix AHV) and implementing it from the ground up. This includes hardware procurement (if on-premises), software installation, and configuration.
Security Integration
Embedding comprehensive security measures into every layer of your private cloud. This includes network segmentation, advanced firewalls, intrusion detection/prevention, robust access controls, data encryption at rest and in transit, and continuous security monitoring.
Scalability and Elasticity
Designing the private cloud to scale seamlessly with your evolving business demands, allowing for easy expansion of resources as needed without significant re-architecture.
Automation and Orchestration
Implementing automation tools and orchestration platforms to streamline resource provisioning, configuration management, and operational tasks, reducing manual effort and improving efficiency.
Integration with Existing Systems
Ensuring seamless integration of your new private cloud infrastructure with existing on-premises systems, applications, and data sources, facilitating a smooth transition and hybrid capabilities if desired.
Disaster Recovery and Backup
Incorporating robust disaster recovery and backup strategies specifically designed for your private cloud, ensuring data protection and business continuity. Our Private Cloud Setup service empowers your organization with a dedicated, secure, and highly controllable cloud environment that meets your specific performance, security, and compliance requirements.
Management and Monitoring
Setting up comprehensive monitoring solutions to track the health, performance, and security of your private cloud environment. We also provide ongoing management and support to ensure continuous operation.
Hybrid Cloud Setup
We provide seamless integration of your on-premises infrastructure with public cloud environments (such as Azure and AWS) to create a flexible and optimized hybrid cloud. This approach allows organizations to leverage the benefits of both worlds: the control and security of a private data center combined with the scalability, agility, and cost-effectiveness of the public cloud. Our service includes:
Connectivity Solutions
Establishing secure and high-performance network connections between your on-premises data centers and public cloud providers. This involves implementing technologies like VPN (Virtual Private Network) for secure tunnels or direct dedicated connections such as AWS Direct Connect and Azure ExpressRoute for consistent, low-latency connectivity.
Workload Placement Strategy
Assisting in determining the optimal placement for your applications and data. This involves identifying which workloads are best suited for the public cloud (e.g., burstable workloads, web applications, disaster recovery sites) and which should remain on-premises (e.g., sensitive data, legacy applications with strict compliance needs).
Unified Management and Orchestration
Implementing tools and platforms that provide a single pane of glass for managing resources across both on-premises and cloud environments. This ensures consistent policy enforcement, simplified operations, and efficient resource allocation. Examples include hybrid management solutions from VMware, Microsoft Azure Arc, and AWS Outposts.
Data Synchronization and Integration
Designing and implementing secure and efficient mechanisms for data transfer and synchronization between on-premises and cloud environments. This ensures data consistency and availability across your hybrid infrastructure.
Identity Federation
Establishing a unified identity and access management (IAM) system that spans your on-premises directory (e.g., Active Directory) and public cloud IAM services (e.g., Azure AD, AWS IAM). This provides a seamless single sign-on experience for users while maintaining centralized control over access privileges.
Security Consistency
Extending your on-premises security policies and controls to your public cloud footprint. This includes consistent network segmentation, firewall rules, intrusion detection, and data encryption across the hybrid environment to maintain a strong security posture.
Disaster Recovery and Business Continuity
Leveraging the hybrid cloud for enhanced disaster recovery capabilities. This involves replicating critical on-premises workloads to the public cloud for rapid failover in case of an outage, significantly improving resilience.
Cost Management for Hybrid Environments
Providing strategies and tools to monitor and optimize costs across your hybrid infrastructure, ensuring you get the most value from both your on-premises investments and public cloud spending. Our Hybrid Cloud Setup service enables your organization to achieve maximum flexibility, agility, and resilience by seamlessly integrating your diverse IT environments, allowing you to innovate faster and respond to changing business demands.
Managed Cloud Security Posture Management
We provide continuous monitoring and improvement of your cloud security posture, ensuring that your cloud environments are always configured securely and in compliance with best practices and regulatory requirements. Cloud Security Posture Management (CSPM) is crucial for identifying and remediating misconfigurations, vulnerabilities, and compliance gaps that often arise in dynamic cloud environments. Our service includes:

Continuous Configuration Monitoring
Automated scanning and analysis of your cloud configurations (e.g., virtual machines, storage accounts, databases, network settings, IAM policies) across all your cloud platforms (e.g., Azure, AWS). This identifies deviations from security baselines and best practices in real-time
Misconfiguration Detection and Remediation
Proactively detecting common cloud misconfigurations, such as publicly exposed storage buckets, overly permissive IAM roles, unencrypted data stores, and insecure network settings. We provide actionable recommendations and, where appropriate, automated remediation to correct these issues.
Compliance and Governance Enforcement
Mapping your cloud environment against various industry standards and regulatory frameworks (e.g., CIS Benchmarks, NIST, ISO 27001, HIPAA, GDPR, PCI DSS). We enforce compliance policies as code and provide continuous reporting on your adherence to these standards.
Vulnerability Management in the Cloud
Integrating with vulnerability scanning tools to identify software vulnerabilities within your cloud instances and applications. This helps prioritize and track remediation efforts.
Identity and Access Governance
Continuously reviewing IAM policies and permissions to ensure the principle of least privilege is enforced, identifying stale accounts, excessive permissions, and potential privilege escalation paths.
Threat Detection and Risk Prioritization
Correlating CSPM findings with threat intelligence to prioritize risks based on their potential impact and exploitability. This helps your security team focus on the most critical issues.
Automated Security Workflows
Implementing automation to streamline security operations, such as automatically creating tickets for misconfigurations, triggering alerts for critical deviations, or initiating automated remediation actions.
Reporting and Dashboards
Providing clear, actionable dashboards and reports that offer a unified view of your cloud security posture, compliance status, and remediation progress across your entire cloud footprint. Our Managed Cloud Security Posture Management service helps you maintain a strong and resilient security posture in the cloud, reducing your attack surface, ensuring compliance, and providing continuous visibility into your cloud security risks.
Managed Cloud Backup

Automated Backup Scheduling
Implementing automated backup schedules tailored to your Recovery Point Objectives (RPOs) and Recovery Time Objectives (RTOs). This ensures that critical data is backed up frequently enough to minimize data loss and that recovery can occur within acceptable timeframes.
Data Scope Definition
Working with you to identify and classify all critical cloud data that requires backup, including data in various cloud services (e.g., virtual machines, databases, object storage, file shares, SaaS applications).
Secure Cloud Storage
Utilizing highly secure and resilient cloud storage services provided by your cloud provider (e.g., Azure Blob Storage, AWS S3) for storing backups. This includes encryption of data at rest and in transit, and robust access controls.
Cross-Region and Cross-Account Backups
Implementing strategies for replicating backups to different geographical regions or separate cloud accounts to enhance resilience against regional outages or account compromise, aligning with the "off-site" principle of the 3-2-1 backup rule.
Data Integrity Verification
Regularly performing integrity checks on backups to ensure that data is not corrupted and can be successfully restored when needed.
Granular Recovery Options
Providing flexible recovery options, allowing you to restore entire systems, specific applications, individual files, or database tables, minimizing recovery time and impact.
Compliance and Retention Policies
Configuring backup and retention policies to meet your specific regulatory compliance requirements (e.g., HIPAA, GDPR) and internal data governance standards.
Regular Testing and Reporting
Periodically testing backup and restore processes to validate their effectiveness and providing detailed reports on backup status, success rates, and compliance. Our Managed Cloud Backup service ensures your cloud data is consistently protected, easily recoverable, and compliant, providing peace of mind and robust business continuity.
Monitoring and Alerting
Continuous monitoring of backup jobs, status, and storage utilization. We set up alerts for any failures or anomalies, ensuring prompt intervention.
Disaster Recovery as a Service (DRaaS)
Our DRaaS offering provides rapid recovery and business continuity in the face of unforeseen events, from natural disasters to cyberattacks. We replicate your critical data and applications to a secure, off-site cloud environment. In the event of an outage, we swiftly failover to the replicated environment, minimizing downtime and data loss. This includes:
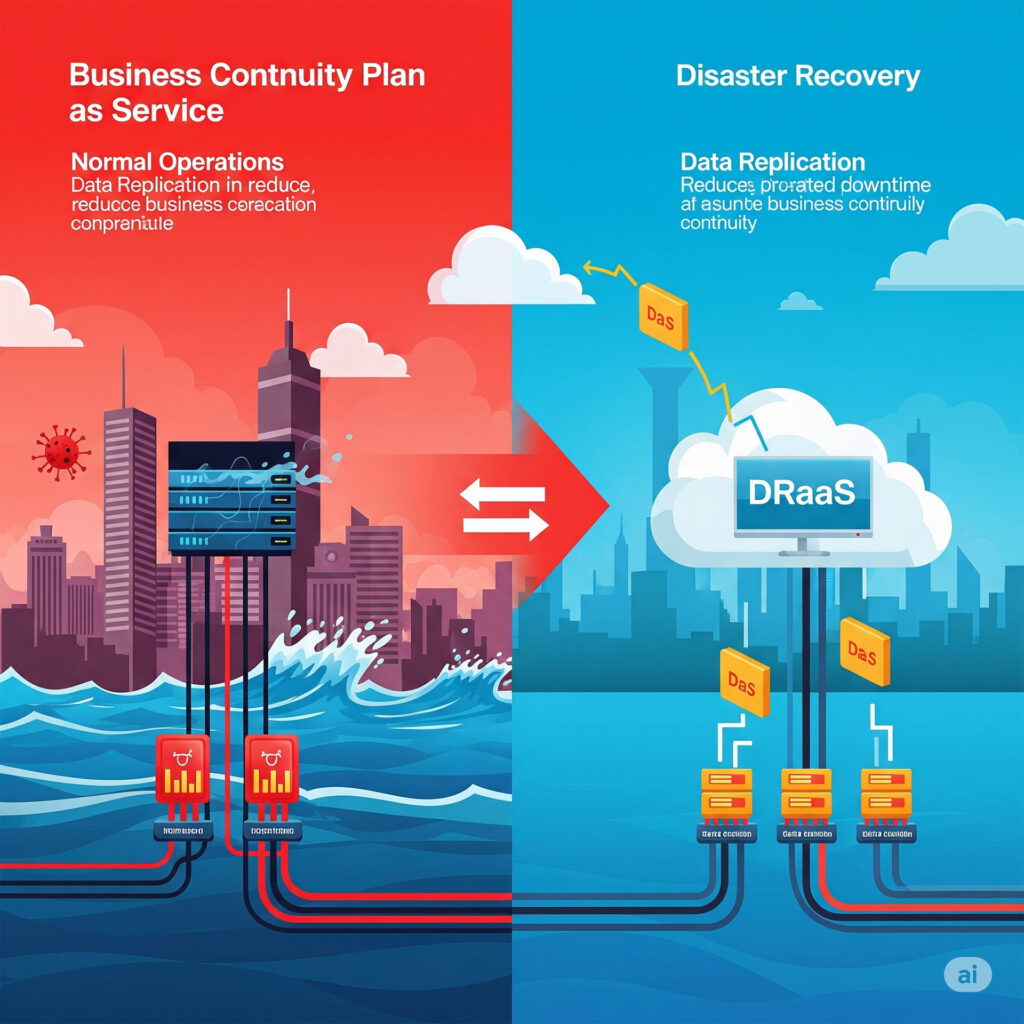
Tailored Recovery Objectives (RTO/RPO)
Defining clear Recovery Time Objectives (RTOs) – the maximum acceptable downtime – and Recovery Point Objectives (RPOs) – the maximum acceptable data loss – based on your business's criticality and risk tolerance for each application and dataset.
Comprehensive Replication Strategies
Implementing continuous or scheduled replication of virtual machines, physical servers, databases, and applications to a designated recovery site in the cloud. This ensures that a near real-time or recent copy of your environment is always available.
Automated Failover and Failback
Designing and configuring automated failover mechanisms to seamlessly switch operations to the cloud recovery site in the event of a disaster. Once the primary site is restored, we manage the failback process to return operations to your original environment with minimal disruption.
Non-Disruptive Testing
Conducting regular, non-disruptive disaster recovery drills to validate the effectiveness of your recovery plans and ensure that all systems can be brought online successfully. This identifies potential issues before a real disaster strikes.
Secure Recovery Environment
Ensuring the cloud recovery environment is as secure as your primary production environment, with appropriate network segmentation, access controls, encryption, and threat protection measures in place.
Monitoring and Management
Providing continuous monitoring of the replication process and the health of the recovery environment. Our team proactively manages the DRaaS solution, addressing any issues to ensure readiness.
Compliance and Reporting
Assisting with documentation and reporting to meet regulatory compliance requirements for disaster recovery, demonstrating your organization's resilience capabilities. Our DRaaS solution empowers your business to withstand disruptions, ensuring your critical operations continue with minimal interruption and data loss, safeguarding your reputation and financial stability.
Performance Optimization
Our Performance Optimization service is dedicated to enhancing the speed, efficiency, and responsiveness of your cloud applications and infrastructure. In the cloud, optimizing performance is not just about speed; it’s about maximizing resource utilization, improving user experience, and controlling costs. Our comprehensive approach includes:
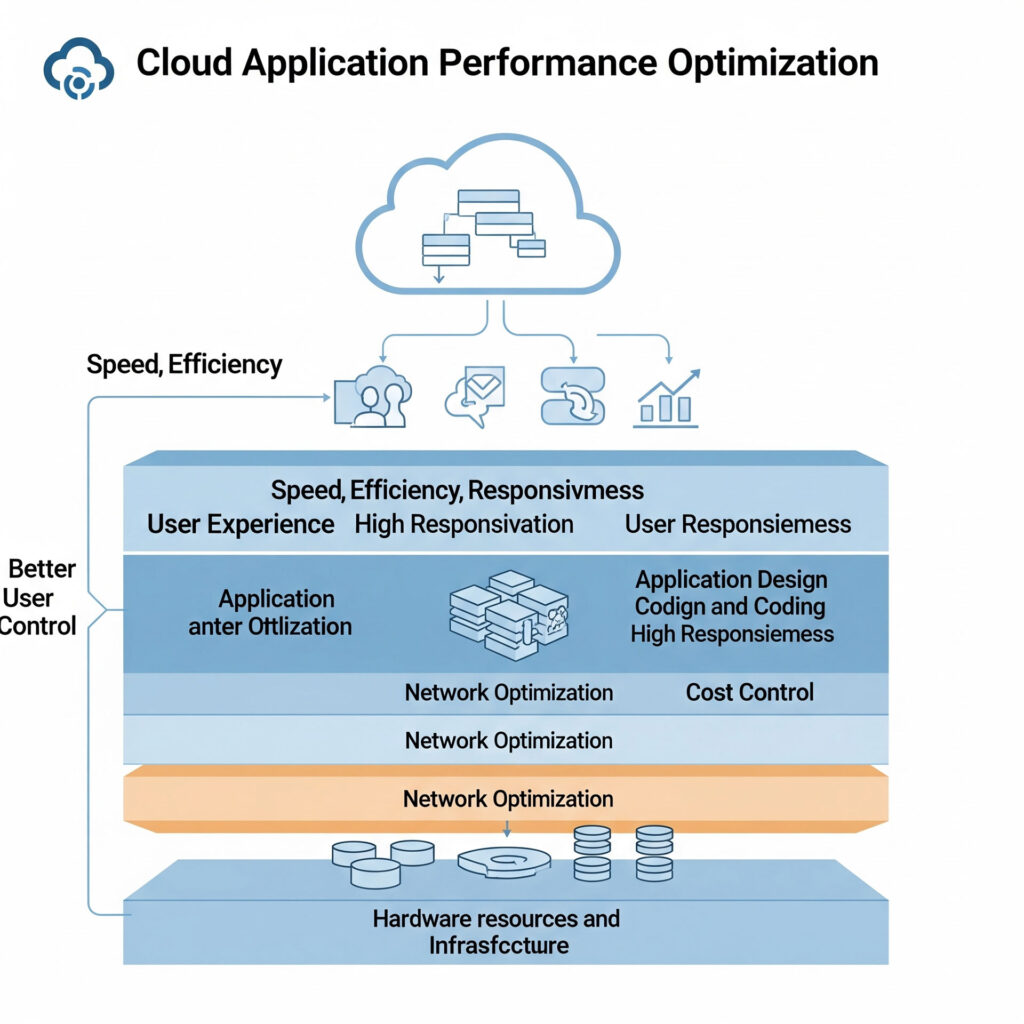
Application Performance Monitoring (APM)
Implementing advanced APM tools to gain deep visibility into your application's performance, identifying bottlenecks, slow transactions, and error rates. This covers everything from code execution to database queries and external service calls.
Resource Right-Sizing
Analyzing your cloud resource consumption (CPU, memory, storage, network I/O) and recommending optimal instance types, storage tiers, and database configurations. This ensures your applications have sufficient resources without over-provisioning, which can lead to unnecessary costs.
Network Optimization
Improving network latency and throughput within your cloud environment and between your cloud and on-premises systems. This involves optimizing network topology, leveraging content delivery networks (CDNs), and configuring load balancers effectively.
Database Performance Tuning
Analyzing database queries, indexing strategies, and schema design to identify and resolve performance issues. This includes optimizing database configurations and leveraging cloud-native database services for scalability and efficiency.
Container and Serverless Optimization
For modern cloud-native applications, we optimize container orchestration (e.g., Kubernetes) for efficient resource scheduling and scaling, and fine-tune serverless functions for optimal execution time and cost.
Caching Strategies
Implementing effective caching mechanisms (e.g., in-memory caches, distributed caches, CDN caching) to reduce database load, improve response times, and enhance user experience.
Code and Architecture Review
Conducting in-depth reviews of your application code and cloud architecture to identify areas for improvement in terms of efficiency, scalability, and resilience. This often involves recommending architectural patterns like microservices or event-driven architectures.
Continuous Monitoring and Iteration
Performance optimization is an ongoing process. We establish continuous monitoring, regular performance testing, and iterative improvements to ensure your cloud applications consistently deliver optimal speed and efficiency as your business evolves. Our Performance Optimization service ensures your cloud applications are not only fast and responsive but also cost-efficient and scalable, providing a superior user experience and supporting your business growth.
Cost-Performance Balance
Striking the right balance between performance and cost. We ensure that performance enhancements are achieved efficiently, avoiding solutions that lead to disproportionately high cloud expenditures.
Cost Management and Optimization
Our Cost Management and Optimization service is designed to help your organization gain full visibility and control over cloud spending, ensuring you maximize your return on investment (ROI) while maintaining optimal performance and security. Cloud costs can quickly escalate without proper management, making this a critical aspect of successful cloud adoption. Our comprehensive approach includes:
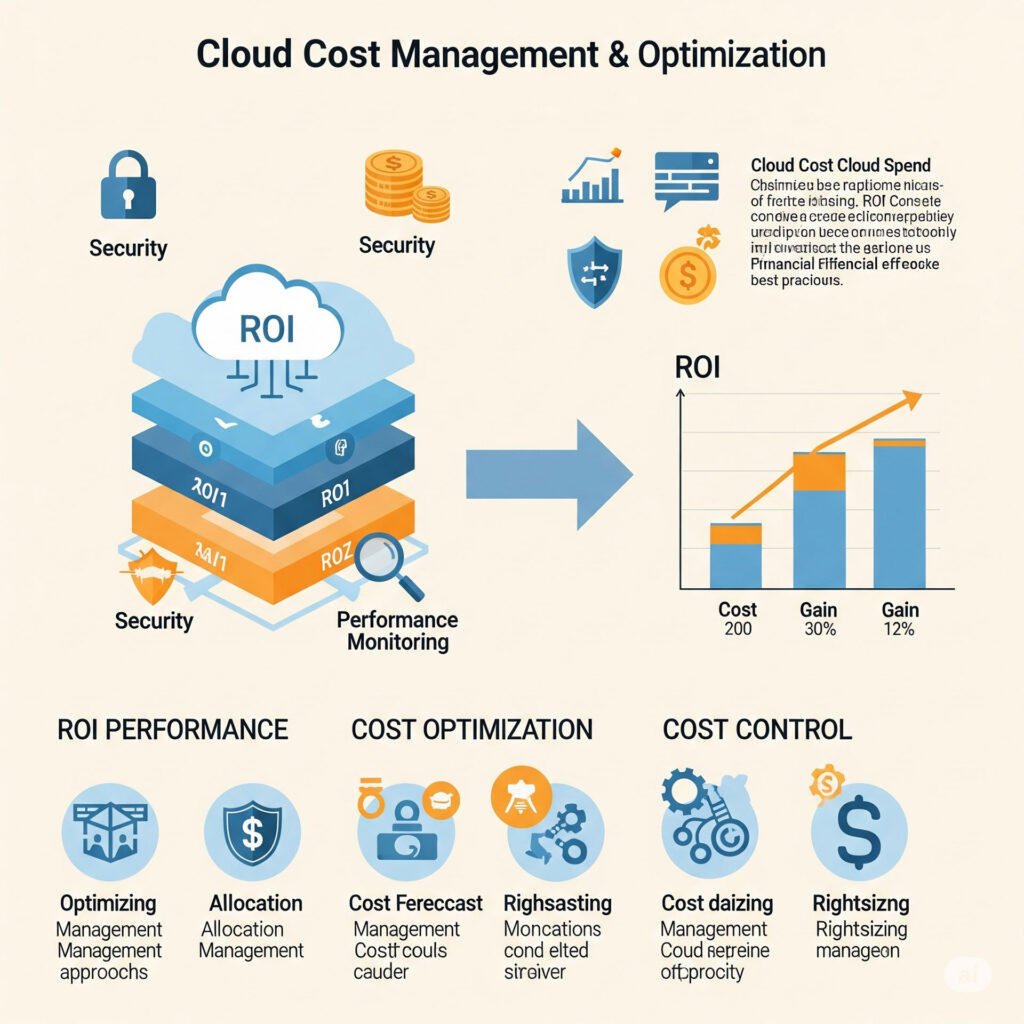
Cloud Cost Visibility and Reporting
Implementing tools and processes to provide granular visibility into your cloud expenditures across all services and departments. This includes detailed dashboards and reports that break down costs by resource, tag, project, and business unit, enabling informed decision-making.
Resource Right-Sizing
Continuously analyzing resource utilization (CPU, memory, storage, network) for virtual machines, databases, and other cloud services. We identify opportunities to right-size resources by downgrading over-provisioned instances or upgrading under-provisioned ones, ensuring optimal performance at the lowest possible cost.
Reserved Instances (RIs) and Savings Plans Management
Strategically recommending and managing the purchase of Reserved Instances (RIs) or Savings Plans for predictable workloads. This allows you to commit to a certain level of usage in exchange for significant discounts compared to on-demand pricing.
Waste Identification and Remediation
Identifying and eliminating cloud waste, such as idle resources, unattached storage volumes, zombie instances, and unused snapshots. We provide recommendations and automated processes to clean up these resources, reducing unnecessary spending.
Automated Cost Governance
Implementing policies and automation rules to enforce cost controls, prevent unauthorized resource creation, and ensure adherence to budgeting guidelines. This includes setting up alerts for budget overruns and enforcing tagging policies for better cost allocation.
Pricing Model Optimization
Advising on the most cost-effective pricing models for various cloud services, including choosing between on-demand, spot instances, reserved instances, and serverless computing based on workload characteristics.
Cloud Architecture Optimization for Cost
Reviewing your cloud architecture to identify design inefficiencies that contribute to higher costs. This might involve recommending changes to network topology, data transfer strategies, or service selection to reduce expenses without compromising performance or security.
Continuous Monitoring and Review
Cloud cost optimization is an ongoing process. We provide continuous monitoring of spending trends, regular cost reviews, and iterative adjustments to ensure sustained cost efficiency as your cloud environment evolves. Our Cost Management and Optimization service transforms your cloud spending from a variable expense into a predictable and optimized investment, ensuring you get the maximum value and ROI from your cloud infrastructure.
FinOps Implementation
Assisting your organization in adopting FinOps (Cloud Financial Operations) principles, fostering collaboration between finance, engineering, and operations teams to drive financial accountability and maximize the business value of your cloud investments.
Private Cloud
In an era where data sovereignty, stringent compliance requirements, and customized IT environments are paramount, many organizations are seeking cloud solutions that offer more control and dedicated resources than typical public cloud offerings. While the public cloud provides unparalleled scalability and convenience, it often comes with shared infrastructure and a level of control that may not suit every business’s unique needs, especially those handling highly sensitive data or operating under strict regulatory frameworks.

This is precisely where our Private Cloud Setup Service from UTCYBER becomes a necessity. A private cloud is a cloud computing environment where all hardware and software resources are dedicated exclusively to a single organization. Whether hosted within your own data center (on-premises) or managed by us in a secure off-site facility, a private cloud delivers the agility and efficiency of cloud computing while providing unparalleled control, enhanced security, and predictable performance.
Our service extends beyond merely deploying the technology. We offer a comprehensive, end-to-end approach to designing, implementing, and optimizing your private cloud infrastructure. From initial needs assessment and architecture design to hardware procurement, software installation, virtualization setup, and ongoing management, we ensure your private cloud is perfectly tailored to your specific business objectives, security posture, and compliance obligations. With our Private Cloud Setup Service, you gain the benefits of cloud agility with the dedicated resources and isolation traditionally found in on-premises environments, giving you the best of both worlds.
Hybrid cloud

A hybrid cloud environment offers the best of both worlds:
Disaster Recovery and Business Continuity
Utilize public cloud resources as a robust and cost-effective solution for disaster recovery and backup, enhancing your resilience against unforeseen events.
Enhanced Agility and Scalability
Gain the ability to "burst" workloads to the public cloud during peak demands, avoiding over-provisioning your private infrastructure. This ensures you can scale rapidly without significant capital expenditure.
Cost Optimization
Achieve a balance between predictable costs of a private cloud and the pay-as-you-go model of public clouds, optimizing overall IT expenditure.
Optimal Workload Placement
It allows you to strategically place different applications and data where they make the most sense. Sensitive data and critical legacy applications might reside in your private cloud for maximum control and compliance, while less sensitive, burstable, or modern applications can leverage the immense scalability, cost-effectiveness, and diverse services of public clouds.
Innovation and Flexibility
Access a wide array of specialized services (e.g., AI/ML, serverless computing, advanced analytics) offered by public cloud providers, accelerating innovation without needing to build and maintain these capabilities in-house.
Our comprehensive Hybrid Cloud Setup Service covers every aspect of this complex integration. We work closely with you to:
Assess and Strategize
Understand your business needs, existing IT landscape, compliance requirements, and application portfolios to design the ideal hybrid cloud architecture.
Network Interconnection
Establish secure, high-performance network connectivity between your private cloud and selected public cloud providers using technologies like VPNs, direct connects, or dedicated interlinks.
Identity and Access Management (IAM) Integration
Implement unified identity management across your hybrid environment for seamless and secure access control.
Data Synchronization and Management
Develop strategies and deploy tools for efficient and secure data transfer, synchronization, and governance across disparate cloud environments
Workload Migration and Orchestration
Assist in migrating applications and data to their optimal cloud locations and set up orchestration tools for unified management and deployment across your hybrid estate.
Security and Compliance Frameworks
Ensure consistent security policies, monitoring, and compliance adherence across your private and public cloud components, leveraging cloud-native security tools and third-party solutions.
By partnering with us, you can confidently navigate the complexities of multi-cloud integration, unlock the full potential of a flexible hybrid environment, and build a future-ready IT infrastructure that drives innovation, enhances resilience, and optimizes costs.
