- Home
- /
- Managed SOC services
Managed SOC services
Endpoint Security
UTCYBER Endpoint Security service provides comprehensive protection for all your devices, including laptops, desktops, servers, mobile phones, and IoT devices, from a wide range of cyber threats. Endpoints are often the primary target for attackers, making robust endpoint security a critical component of your overall cybersecurity strategy. Our service includes:
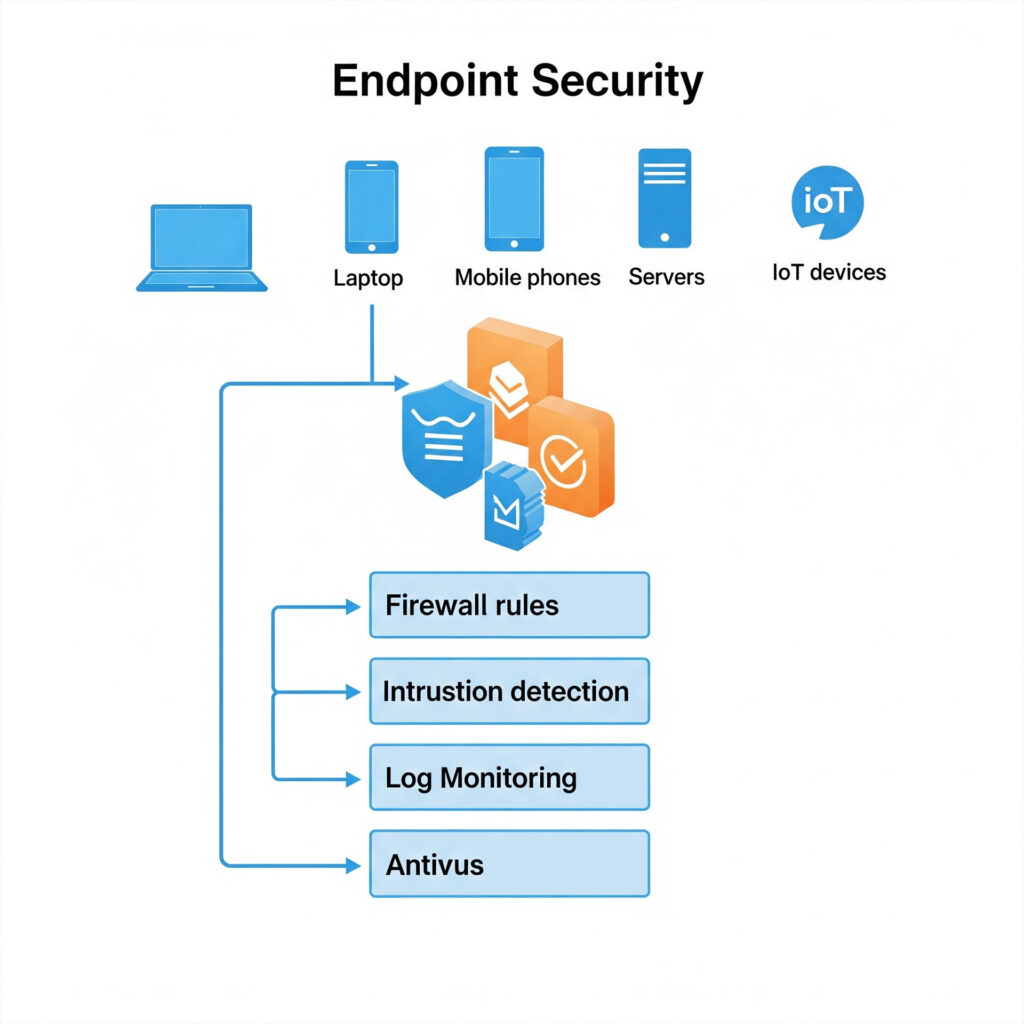
Advanced Threat Protection: Deploying next-generation antivirus (NGAV) and anti-malware solutions that use advanced techniques like machine learning, behavioral analysis, and artificial intelligence to detect and block known and unknown threats, including ransomware, zero-day exploits, and fileless malware.
Endpoint Detection and Response (EDR): Implementing EDR solutions that continuously monitor endpoint activity, collect telemetry data, and provide deep visibility into potential threats. EDR enables rapid detection, investigation, and response to sophisticated attacks that may bypass traditional defenses.
Managed Detection and Response (MDR) Integration: For enhanced protection, our Endpoint Security service can be integrated with our broader Managed Detection and Response (MDR) offerings, providing 24/7 monitoring, threat hunting, and expert-led incident response across your endpoints.
Vulnerability Management: Regularly scanning endpoints for software vulnerabilities, misconfigurations, and outdated patches. We provide prioritized recommendations and assist with the remediation process to reduce the attack surface.
Host-Based Firewall Management: Configuring and managing host-based firewalls on endpoints to control network traffic and prevent unauthorized access to devices.
Device Control and Data Loss Prevention (DLP): Implementing policies to control the use of removable media and other peripherals, and deploying DLP solutions to prevent sensitive data from leaving your organization's endpoints, whether intentionally or accidentally.
Application Control and Whitelisting: Implementing policies to restrict which applications can run on endpoints, preventing the execution of unauthorized or malicious software.
Security Awareness and Training: Providing guidance and resources to educate your employees on endpoint security best practices, such as identifying phishing attempts and safe browsing habits, as the human element remains a key factor in endpoint security.
Centralized Management and Reporting: Providing a centralized platform for managing all endpoint security policies, monitoring alerts, and generating reports on security posture and incident response activities. Our Endpoint Security service ensures that your devices are continuously protected, monitored, and managed, significantly reducing the risk of endpoint-based attacks and safeguarding your valuable data and operations.
Network Security
Cyber Protection
Threat Intelligence
Endpoint Security
Network Analysis
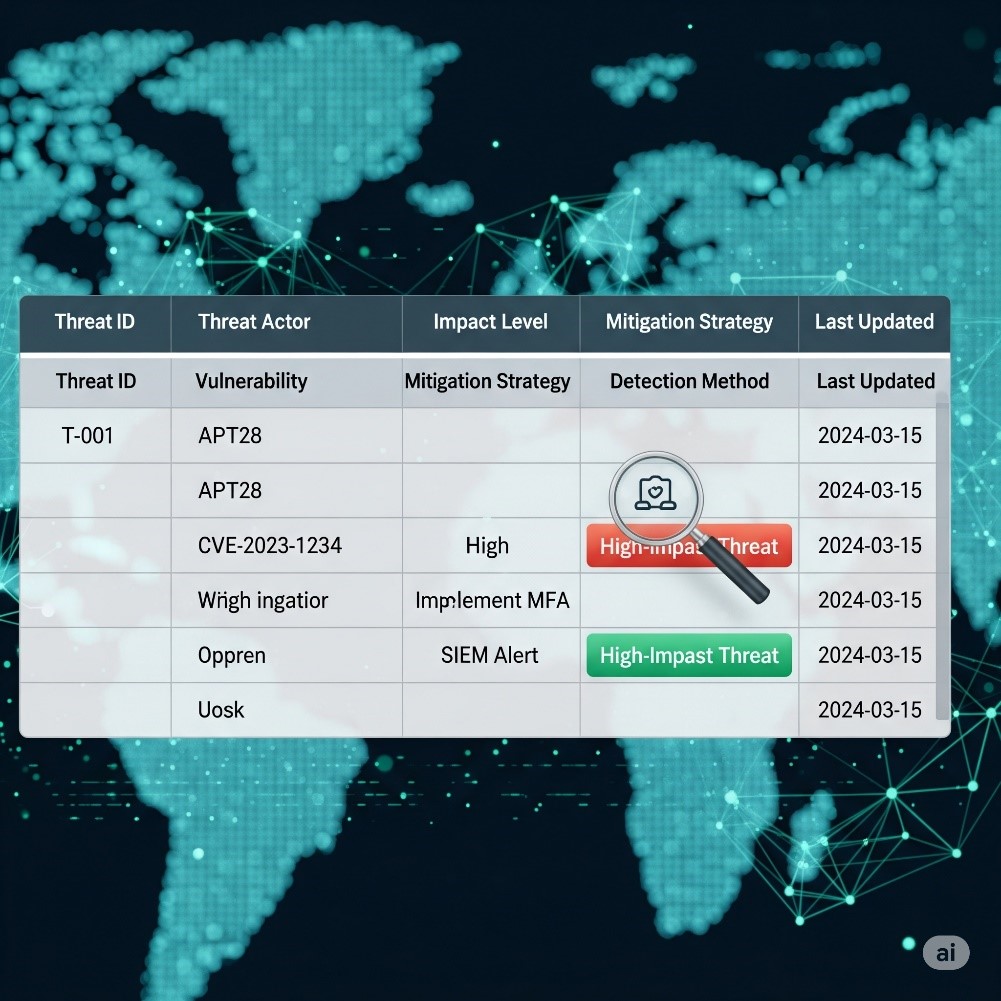
Threat Hunting/Threat Intelligence
Our Threat Hunting/Threat Intelligence service provides a proactive and intelligence-driven approach to cybersecurity, moving beyond reactive defense mechanisms to actively seek out and neutralize hidden threats before they can cause significant damage. This dual-pronged strategy ensures your organization stays ahead of evolving cyber adversaries. Our service includes:
Proactive Threat Hunting
Hypothesis-Driven Hunting
Developing specific hypotheses about potential threats based on threat intelligence, attacker TTPs (Tactics, Techniques, and Procedures), and observed anomalies.
Data Analysis and Correlation
Deeply analyzing security logs, network traffic, endpoint data, and other telemetry from various sources (SIEM, EDR, network devices) to identify subtle indicators of compromise (IoCs) and suspicious activities.
Behavioral Anomaly Detection
Utilizing advanced analytics and machine learning to identify deviations from normal user and system behavior, which can indicate compromised accounts, insider threats, or novel attack techniques.
Tooling and Techniques
Employing specialized threat hunting tools, custom scripts, and advanced query languages (e.g., KQL for Azure Sentinel) to efficiently navigate large datasets and uncover hidden threats.
Actionable Threat Intelligence
We provide curated and contextualized threat intelligence that informs and enhances your security posture. This includes:
Collection and Aggregation
Gathering intelligence from a wide array of sources, including open-source intelligence (OSINT), commercial threat feeds, dark web monitoring, and industry-specific intelligence sharing platforms.
Analysis and Contextualization
Analyzing raw threat data to identify relevant threats, understand attacker motivations, capabilities, and common attack vectors. We contextualize this intelligence to your specific industry, assets, and threat landscape.
Indicators of Compromise (IoCs)
Delivering timely IoCs (e.g., malicious IP addresses, domain names, file hashes, URLs) that can be immediately integrated into your security tools for enhanced detection.
Tactics, Techniques, and Procedures (TTPs)
Providing insights into the methods and strategies used by threat actors, enabling your team to anticipate attacks and build more resilient defenses.
Vulnerability Intelligence
Supplying information on newly discovered vulnerabilities and their potential exploitation, allowing for proactive patching and mitigation.
Integration and Feedback Loop
We integrate threat intelligence directly into your security operations and threat hunting efforts. Findings from threat hunts are then fed back into our intelligence gathering process, creating a continuous feedback loop that refines our understanding of the threat landscape and improves future detections. Our Threat Hunting/Threat Intelligence service transforms your defense from reactive to proactive, significantly reducing the dwell time of attackers, minimizing potential damage, and strengthening your overall cybersecurity resilience.
Database Activity Monitoring:
In today’s interconnected digital landscape, organizations heavily rely on databases to store and manage their most critical assets – sensitive data. However, this centralization of valuable information also makes databases prime targets for cyberattacks, insider threats, and accidental misuse. Traditional security measures, while essential, often fall short in providing the granular visibility and real-time protection needed to truly safeguard these vital repositories.

This is where Database Activity Monitoring (DAM) services from UTCYBER become indispensable. DAM is a specialized cybersecurity solution designed to continuously observe, record, and analyze all activities occurring within database systems. It goes beyond simple access logs, providing a comprehensive, independent audit trail of who is accessing what data, when, where, and how. By offering real-time insights into user behavior, SQL queries, schema changes, and data modifications, DAM empowers organizations to proactively detect and respond to suspicious activities, enforce compliance policies, and prevent data breaches before they can inflict significant damage. Our DAM service acts as a vigilant guardian, ensuring the integrity, confidentiality, and availability of your critical data assets.
Incident Management
Our Incident Management service provides a structured and efficient approach to handling security incidents, from initial detection to post-incident analysis. Swift and effective incident response is crucial for minimizing the impact of cyberattacks, reducing downtime, protecting sensitive data, and maintaining business continuity. Our service covers the following key phases:
Preparation
Team Readiness
Ensuring your incident response team (internal or our managed experts) is trained, equipped, and ready to act.
Incident Response Planning
Developing and maintaining a comprehensive incident response plan (IRP) tailored to your organization's specific environment, assets, and potential threats. This includes defining roles, responsibilities, communication protocols, and escalation paths.
Tooling and Infrastructure
Setting up and maintaining the necessary security tools (e.g., SIEM, EDR, forensic tools) and infrastructure to support effective incident response.
Identification
Continuous Monitoring
Leveraging security monitoring tools (SIEM, XDR) and threat intelligence to detect suspicious activities, anomalies, and indicators of compromise (IoCs) in real-time.
Alert Triage and Validation
Rapidly triaging security alerts to distinguish true positives from false positives and validating potential incidents.
Containment
Isolation
Taking immediate steps to isolate affected systems, networks, or applications to prevent the further spread of the attack. This might involve network segmentation, blocking malicious IPs, or quarantining compromised endpoints.
Damage Control
Minimizing the immediate impact of the incident on business operations and data.
Eradication
Threat Removal
Thoroughly removing the root cause of the incident and all traces of the attacker from your environment. This includes patching vulnerabilities, removing malware, and resetting compromised credentials.
System Hardening
Implementing additional security measures to prevent similar attacks in the future.
Recovery
Restoration
Bringing affected systems and data back online in a secure and controlled manner, prioritizing critical business functions. This often involves restoring from clean backups.
Validation
Verifying that systems are fully functional, secure, and free from any remaining threats.
Post-Incident Analysis (Lessons Learned):
Root Cause Analysis
Conducting a detailed investigation to understand how the incident occurred, what vulnerabilities were exploited, and what controls failed.
Improvement Recommendations
Developing actionable recommendations to enhance your security posture, update policies, improve detection capabilities, and refine incident response procedures to prevent recurrence. Our Incident Management service ensures your organization can respond to security incidents systematically and effectively, minimizing disruption, protecting your assets, and continuously improving your resilience against future cyber threats.
Documentation
Documenting the entire incident, including timelines, actions taken, and outcomes.
DNS Security
Our DNS Security service protects your Domain Name System (DNS) infrastructure from various malicious activities. We defend against attacks like DNS spoofing, DDoS attacks on DNS servers, and DNS tunneling. The service includes DNS filtering to block malicious domains, implements DNSSEC for data authenticity, and continuously monitors traffic for anomalies. By integrating threat intelligence and securing both recursive and authoritative DNS, we ensure reliable and secure internet access for your organization

Protection Against DNS-Based Attacks
Implementing robust defenses against various DNS attack vectors, such as:
DDoS Attacks on DNS Infrastructure
Protecting your authoritative and recursive DNS servers from Distributed Denial of Service (DDoS) attacks that aim to overwhelm and shut down DNS services, making your websites and applications unreachable.
DNS Spoofing/Cache Poisoning
Preventing attackers from injecting forged DNS records into resolvers' caches, which could redirect users to malicious websites.
DNS Tunneling
Detecting and blocking the exfiltration of data or command-and-control communications hidden within legitimate DNS queries.
NXDOMAIN Attacks
Mitigating attacks that flood DNS servers with requests for non-existent domains, leading to resource exhaustion.
DNS Filtering and Content Security
Zero Day Attack Prevention:
Our Zero Day Attack Prevention service focuses on defending your systems and data against previously unknown vulnerabilities, often referred to as “zero-day exploits.” These are critical threats because they exploit flaws for which no patch or public information exists, making traditional signature-based security solutions ineffective. Our approach combines advanced technologies and proactive strategies to anticipate and mitigate these sophisticated attacks:

Heuristic and Anomaly Detection
Utilizing heuristic analysis to identify characteristics of malicious behavior, even if the specific exploit is unknown. This involves looking for patterns that deviate from normal operations, such as attempts to bypass security controls or unexpected code execution.
Behavioral Analysis and Machine Learning
Employing advanced behavioral analysis and machine learning algorithms to detect anomalous or suspicious activities that indicate a zero-day attack, rather than relying on known signatures. This includes monitoring for unusual process behavior, unauthorized system modifications, and abnormal network communications.
Exploit Prevention Technologies
Deploying specialized exploit prevention technologies that focus on blocking the techniques used by zero-day exploits, regardless of the specific vulnerability. This includes memory protection, control flow integrity, and anti-exploitation techniques.
Sandboxing and Isolation
Implementing sandboxing environments to isolate suspicious files or processes, allowing them to run in a controlled environment where their behavior can be analyzed without risking the production system. This helps identify and contain zero-day malware.
MITRE ATT&CK
This is precisely where the MITRE ATT&CK® framework comes into play, and why UTCYBER leverages it as a foundational element of our offerings. MITRE ATT&CK (Adversarial Tactics, Techniques, and Common Knowledge) is a globally accessible, comprehensive knowledge base of real-world adversary behaviors, meticulously documented based on observed cyberattacks. It provides a common language and a structured methodology to understand how attackers operate, detailing their tactics (their objectives, like "Initial Access" or "Persistence") and the specific techniques and procedures (TTPs) they employ to achieve those objectives.
Our MITRE ATT&CK service framework translates this invaluable intelligence into actionable security improvements for your organization. By aligning your defenses with known adversary behaviors, we empower you to move beyond simply reacting to threats. We help you proactively identify gaps in your security controls, prioritize investments, enhance your threat detection and hunting capabilities, and develop more robust incident response plans, all informed by the very methods used by real-world attackers. With our expertise, the MITRE ATT&CK framework becomes more than just a reference; it becomes a strategic blueprint for building a resilient, threat-informed cyber defense.
Application Security

Managed Detection and Response (MDR)
Our Managed Detection and Response (MDR) service provides 24/7 monitoring, advanced threat detection, and rapid response capabilities, acting as an extension of your security team. MDR goes beyond traditional managed security services by actively hunting for threats and providing expert-driven incident response, significantly enhancing your organization’s ability to defend against sophisticated cyberattacks. Our comprehensive MDR service includes:
24/7 Threat Monitoring
Continuous, round-the-clock monitoring of your entire IT environment, including endpoints, networks, cloud infrastructure, and logs. Our security operations center (SOC) analysts leverage advanced tools and expertise to detect suspicious activities in real-time
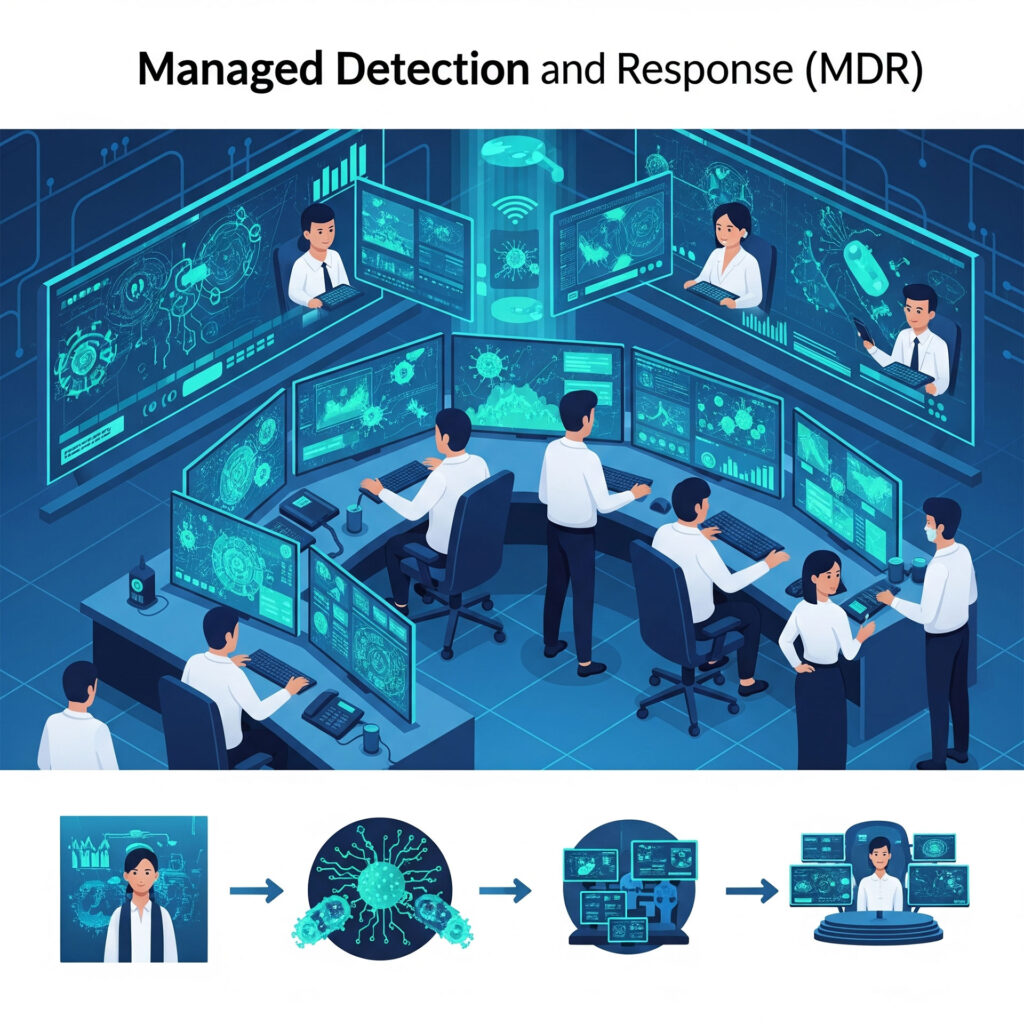
Advanced Threat Detection
Employing a combination of technologies and techniques to identify even the most elusive threats:
Endpoint Detection and Response (EDR):
Utilizing EDR platforms to collect rich telemetry data from endpoints, providing deep visibility into processes, network connections, and file activities to detect malicious behavior.
Network Detection and Response (NDR)
Monitoring network traffic for anomalies, suspicious patterns, and indicators of compromise that might signal an attack or unauthorized activity.
Cloud Security Monitoring
Integrating with cloud-native security tools and logs (e.g., Azure Security Center, AWS GuardDuty) to provide visibility and detect threats across your cloud environments.
User and Entity Behavior Analytics (UEBA)
Leveraging AI and machine learning to establish baselines of normal behavior for users and systems, identifying deviations that could indicate compromised accounts or insider threats.
Threat Intelligence Integration
Incorporating real-time threat intelligence feeds to identify known malicious indicators and emerging attack techniques.
Proactive Threat Hunting
Our expert threat hunters actively search for hidden threats that may have bypassed automated defenses. This involves developing hypotheses, analyzing raw data, and using advanced queries to uncover sophisticated and persistent threats.
Rapid Incident Response
When a threat is detected, our team provides immediate, expert-led response actions:
Alert Validation and Triage
Quickly validating alerts to reduce false positives and prioritize genuine threats.
Investigation and Analysis
Conducting in-depth investigations to understand the scope, nature, and impact of the incident.
Containment and Eradication
Taking swift actions to contain the threat (e.g., isolating endpoints, blocking malicious IPs) and eradicate it from your environment.
Remediation Guidance
Providing clear, actionable guidance to your internal teams for full remediation and recovery.
Security Expertise and Augmentation
Our MDR service provides access to a team of highly skilled security analysts, threat hunters, and incident responders, augmenting your existing security capabilities without the need for significant internal investment.
Reporting and Recommendations
Delivering regular reports on your security posture, detected threats, and incident response activities, along with actionable recommendations for continuous security improvement. Our Managed Detection and Response (MDR) service provides a robust, human-led, and technology-driven solution for comprehensive threat detection and rapid response, significantly reducing your organization's risk exposure and improving your overall cybersecurity resilience.
Security Information and Event Management (SIEM) as a Service:
Our Security Information and Event Management (SIEM) as a Service offers a centralized, cloud-based solution for collecting, analyzing, and managing security logs and events from across your entire IT infrastructure. This service provides comprehensive security insights, enabling proactive threat detection, rapid incident response, and simplified compliance management without the burden of managing complex on-premises SIEM infrastructure. Our SIEM as a Service includes:
Centralized Log Collection and Aggregation: Automatically ingesting security logs and event data from diverse sources, including:
- 1. Network Devices: Firewalls, routers, switches, intrusion detection/prevention systems (IDS/IPS).
- 2. Servers: Operating system logs (Windows Event Logs, Linux Syslog).
- 3. Applications: Web servers, databases, enterprise applications.
- 4. Endpoints: Desktops, laptops, mobile devices.
- 5. Cloud Environments: Logs from public cloud platforms (Azure, AWS, Google Cloud) and SaaS applications. This creates a single, unified repository for all your security-relevant data.
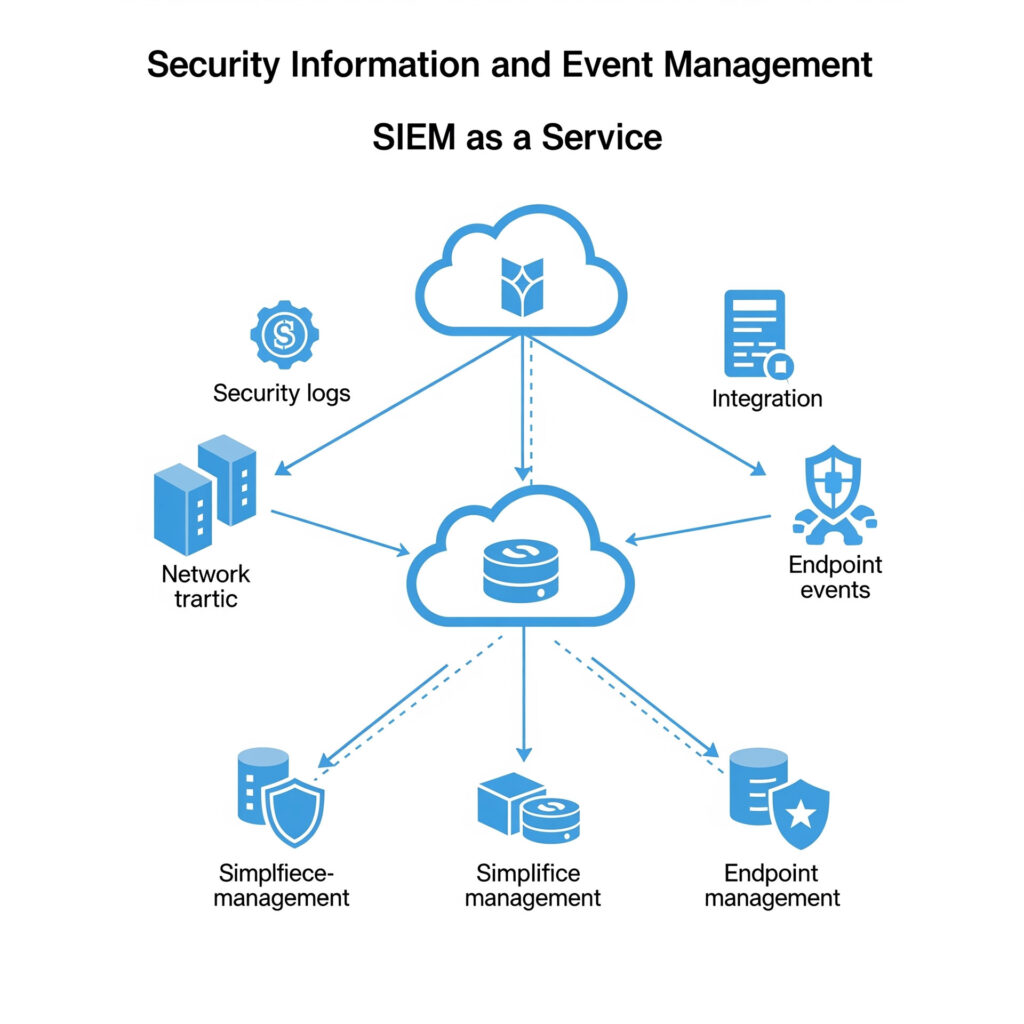
Real-time Event Correlation and Analysis
Leveraging advanced analytics, machine learning, and predefined correlation rules to analyze incoming log data in real-time. This identifies patterns, anomalies, and potential security incidents that might otherwise go unnoticed across disparate log sources.
Threat Detection and Alerting
Automatically detecting known threats, suspicious activities, and indicators of compromise (IoCs) based on correlation rules, behavioral analysis, and integrated threat intelligence. High-fidelity alerts are generated and prioritized, notifying your security team of critical incidents.
Security Incident Management Support
Providing a platform for security analysts to investigate alerts, drill down into raw log data, and manage the lifecycle of security incidents. This streamlines the incident response process and reduces Mean Time To Detect (MTTD) and Mean Time To Respond (MTTR).
Compliance Reporting and Auditing
Generating comprehensive reports and dashboards that demonstrate compliance with various regulatory standards (e.g., GDPR, HIPAA, PCI DSS, SOX, ISO 27001). The centralized log data provides an immutable audit trail for forensic investigations and regulatory audits.
Managed Service Benefits
Our expert security analysts manage the SIEM platform, including rule tuning, threat intelligence updates, and platform maintenance, allowing your internal teams to focus on core business functions and high-priority security tasks. Our SIEM as a Service provides your organization with a powerful, scalable, and cost-effective solution for comprehensive security visibility, enabling proactive threat management and robust compliance adherence.
Scalability and Cost-Effectiveness
As a cloud-native service, it offers elastic scalability to handle growing volumes of log data without requiring significant upfront hardware investments or ongoing maintenance. This translates to a more predictable and often lower total cost of ownership compared to traditional on-premises SIEM deployments.
Managed Vulnerability Management:
Our Managed Vulnerability Management service provides continuous identification and remediation of security weaknesses across your IT environment, significantly reducing your organization’s attack surface. Vulnerabilities are flaws in software, hardware, or configurations that attackers can exploit. Proactive and ongoing management of these weaknesses is essential to prevent breaches. Our service includes:
Continuous Vulnerability Scanning: Regularly scanning your networks, systems, applications, and cloud environments to identify known vulnerabilities. This includes:
- 1. Internal and External Scans: Assessing both internet-facing assets and internal network infrastructure.
- 2. Web Application Scans: Identifying vulnerabilities specific to web applications (e.g., SQL injection, cross-site scripting).
- 3. Cloud Configuration Scans: Detecting misconfigurations in cloud services that could expose your data or systems.
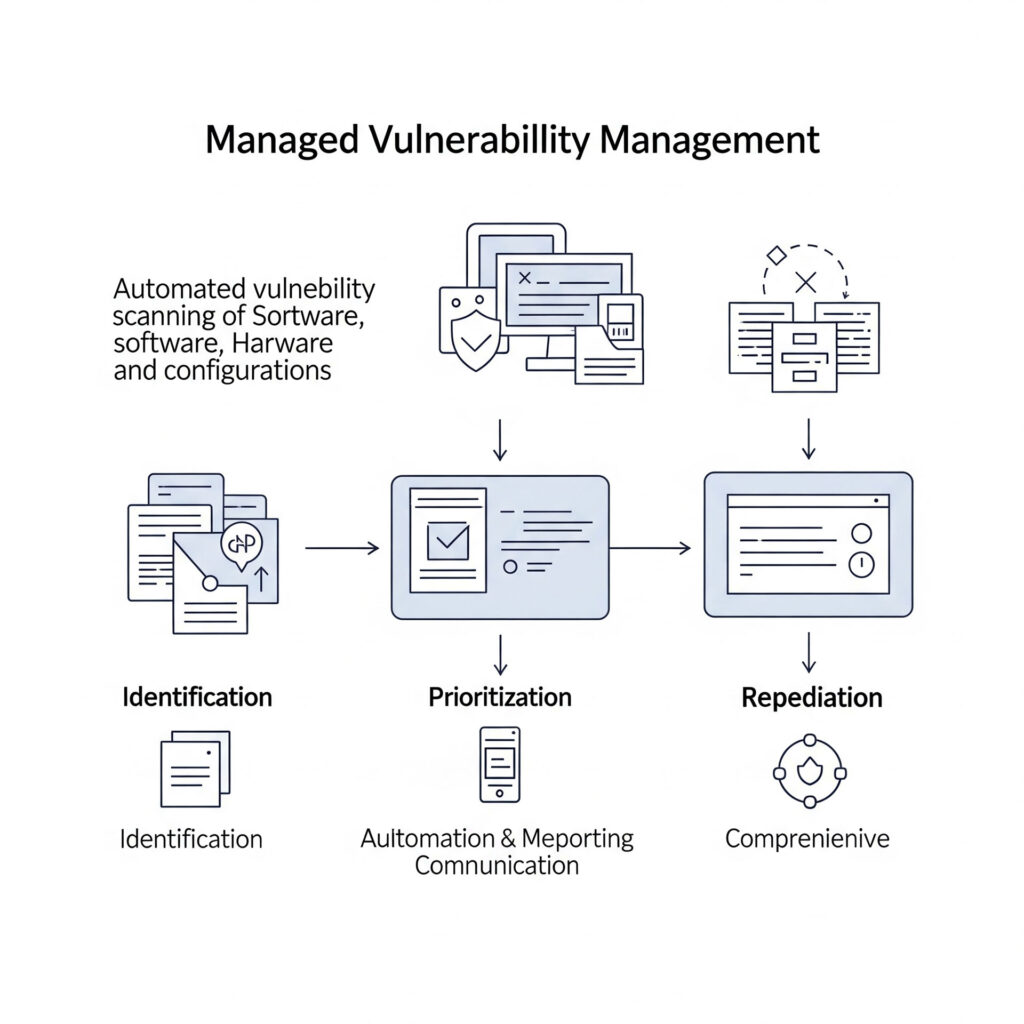
Vulnerability Prioritization
Beyond simply identifying vulnerabilities, we prioritize them based on their severity, exploitability, and potential impact on your business-critical assets. This ensures that your team focuses on addressing the most significant risks first.
Threat Intelligence Integration
Leveraging up-to-date threat intelligence to understand which vulnerabilities are actively being exploited in the wild, further refining prioritization and accelerating remediation efforts.
Patch Management Integration
Working in conjunction with your patch management processes to ensure timely application of security updates to operating systems and applications.
Remediation Guidance and Support
Providing clear, actionable recommendations for patching, configuration changes, and other remediation steps. We can also assist your internal teams in implementing these fixes or manage the remediation process directly.
Compliance Reporting
Generating reports that demonstrate your organization's adherence to regulatory requirements and industry standards related to vulnerability management (e.g., PCI DSS, ISO 27001).
Security Posture Improvement
Continuously working to improve your overall security posture by identifying systemic weaknesses and recommending architectural or process changes that reduce future vulnerabilities. Our Managed Vulnerability Management service provides a proactive, continuous, and expert-driven approach to identifying and mitigating security weaknesses, significantly enhancing your organization's resilience against cyberattacks and ensuring a stronger security posture.
Performance Metrics and Trend Analysis
Tracking key metrics such as the number of open vulnerabilities, average time to remediation, and overall reduction in attack surface. This provides insights into the effectiveness of your vulnerability management program over time.
Security Assessments and Audits with Penetration Testing Services:
Our Security Assessments and Audits with Penetration Testing Services offer a comprehensive and multi-faceted approach to evaluating your organization’s cybersecurity posture. This service moves beyond theoretical checks to simulate real-world attack scenarios, providing a true measure of your defenses.
Thorough Evaluation of Your Security: This refers to a deep dive into your entire IT landscape to identify vulnerabilities, misconfigurations, and weaknesses across various layers. This includes:
- 1. Vulnerability Assessments: Automated and manual scans to detect known security flaws in your systems, applications, and network devices. This identifies potential entry points for attackers.
- 2. Security Audits: A systematic review of your security policies, procedures, and controls against established industry standards (e.g., ISO 27001, NIST, PCI DSS) and regulatory requirements. This ensures compliance and highlights gaps in your security framework.
- 3. Configuration Reviews: Examination of security settings on servers, network devices, cloud environments, and applications to ensure they adhere to best practices and minimize attack surface.
- 4. Risk Assessments: Analyzing the likelihood and potential impact of identified vulnerabilities being exploited, allowing for prioritized remediation efforts based on business criticality.
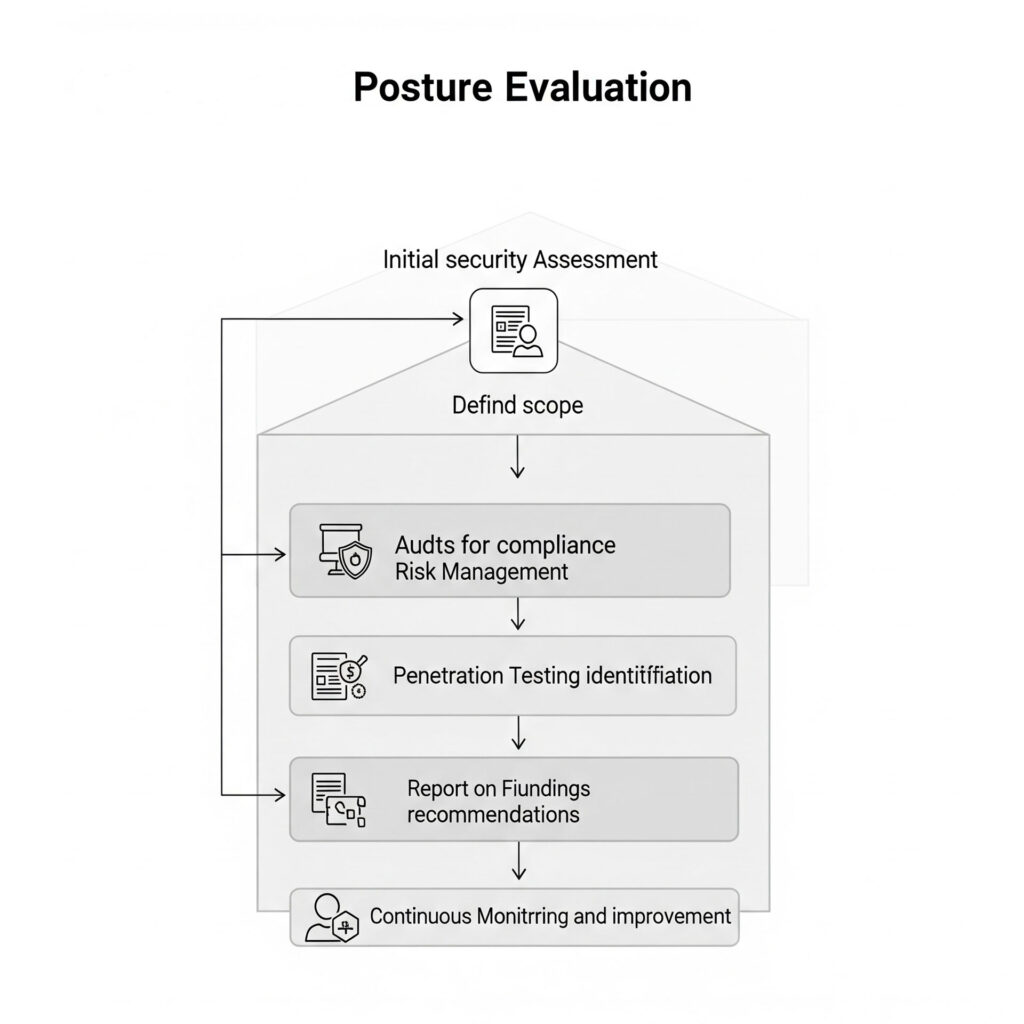
Real-World Attack Simulations (Penetration Testing)
This is the “active” component of the service, where our ethical hackers simulate actual cyberattacks against your systems, applications, and networks. The goal is to safely exploit vulnerabilities to demonstrate how a real attacker could breach your defenses. This includes various types of penetration tests:
External Penetration Testing
Simulating attacks from outside your network (e.g., from the internet) to identify vulnerabilities in your perimeter defenses.
Mobile Application Penetration Testing
Assessing the security of your mobile applications on various platforms.
Internal Penetration Testing
Simulating attacks from within your network, often to assess the impact of a compromised internal system or an insider threat.
Web Application Penetration Testing
Focusing specifically on web applications to uncover vulnerabilities like SQL injection, cross-site scripting (XSS), broken authentication, and other common web application flaws.
Social Engineering Testing
Simulating phishing, pretexting, or other human-centric attacks to evaluate employee susceptibility to social engineering tactics. The value of this service lies in its ability to provide actionable insights into your true security resilience. By undergoing these rigorous evaluations and simulations, you gain a clear understanding of your most critical weaknesses, enabling you to proactively strengthen your defenses and reduce your overall risk exposure before malicious actors can exploit them.
Continuous Security Architecture Review
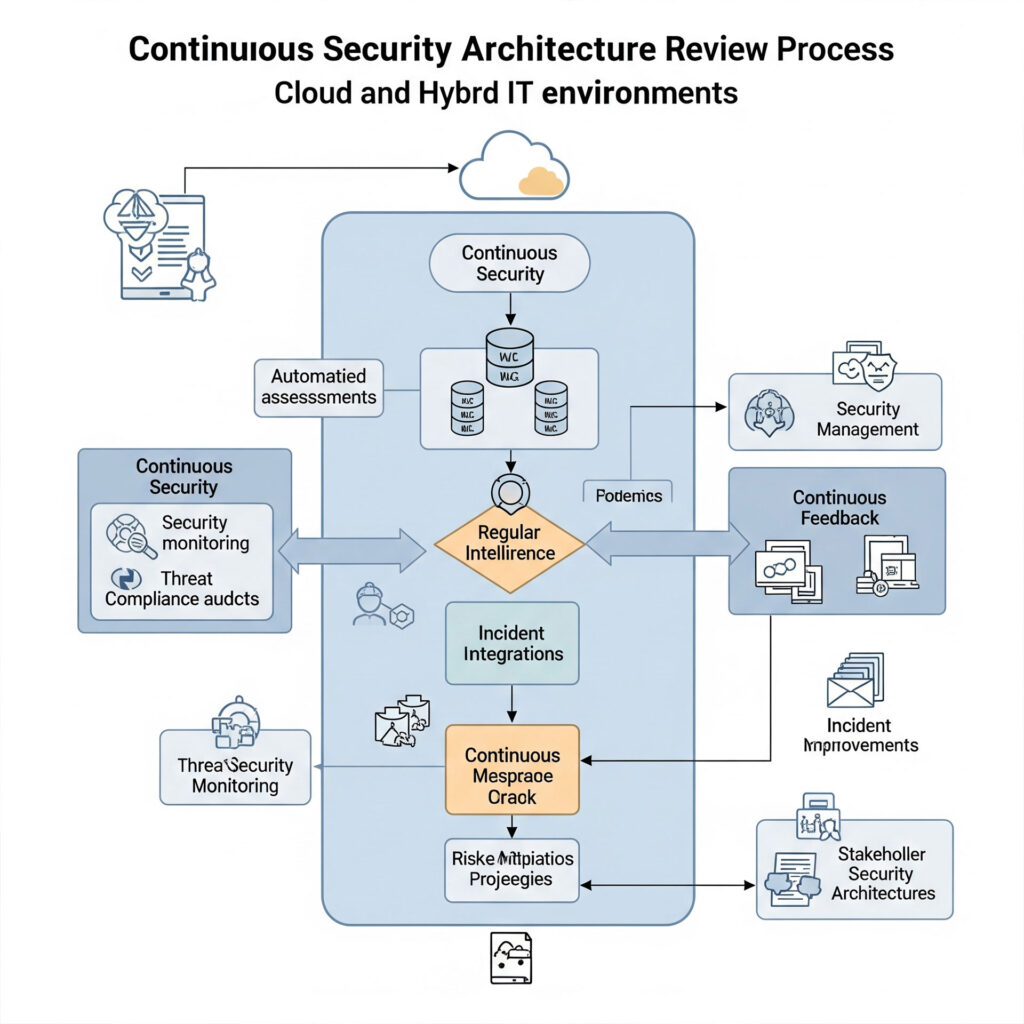
Threat Modeling and Risk Analysis
Applying threat modeling techniques to new and existing architectural components to identify potential attack vectors and assess associated risks. This helps in proactively designing security into your systems rather than retrofitting it.
Proactive Identification of Architectural Gaps
Regularly reviewing your existing and planned IT architectures (network, application, data, cloud, identity) to identify potential security weaknesses, design flaws, and areas where security controls could be enhanced or optimized. This includes assessing the security implications of new technologies or business initiatives.
Alignment with Security Standards and Frameworks
Ensuring your security architecture adheres to relevant industry standards (e.g., NIST, ISO 27001, CIS Benchmarks) and regulatory requirements (e.g., GDPR, HIPAA). We help you maintain compliance as your architecture evolves.
Review of Security Controls Effectiveness
Assessing whether implemented security controls (e.g., firewalls, IDS/IPS, IAM solutions, encryption) are properly configured, effectively deployed, and performing as intended across your architecture.
Optimization for Cloud and Hybrid Environments
Specializing in reviewing security architectures for complex cloud and hybrid cloud deployments, ensuring consistent security policies and controls across diverse platforms (on-premises, private cloud, Azure, AWS, etc.). This addresses challenges like fragmented visibility and inconsistent security postures.
Integration with DevOps and CI/CD Pipelines
Providing guidance on integrating security into your development and operations (DevOps) processes and Continuous Integration/Continuous Delivery (CI/CD) pipelines, promoting a "security by design" approach.
Review of Security Controls Effectiveness
Assessing whether implemented security controls (e.g., firewalls, IDS/IPS, IAM solutions, encryption) are properly configured, effectively deployed, and performing as intended across your architecture.
Optimization for Cloud and Hybrid Environments
Specializing in reviewing security architectures for complex cloud and hybrid cloud deployments, ensuring consistent security policies and controls across diverse platforms (on-premises, private cloud, Azure, AWS, etc.). This addresses challenges like fragmented visibility and inconsistent security postures.
Recommendations for Improvement
Delivering actionable recommendations for architectural enhancements, control implementations, and process improvements to strengthen your security posture. These recommendations are prioritized based on risk and business impact.
Documentation and Knowledge Transfer
Maintaining comprehensive documentation of your security architecture and providing knowledge transfer to your internal teams, fostering a culture of security awareness and continuous improvement. Our Continuous Security Architecture Review service ensures that security is not an afterthought but an integral, evolving component of your IT infrastructure, providing a resilient foundation against current and future cyber threats.
SOAR
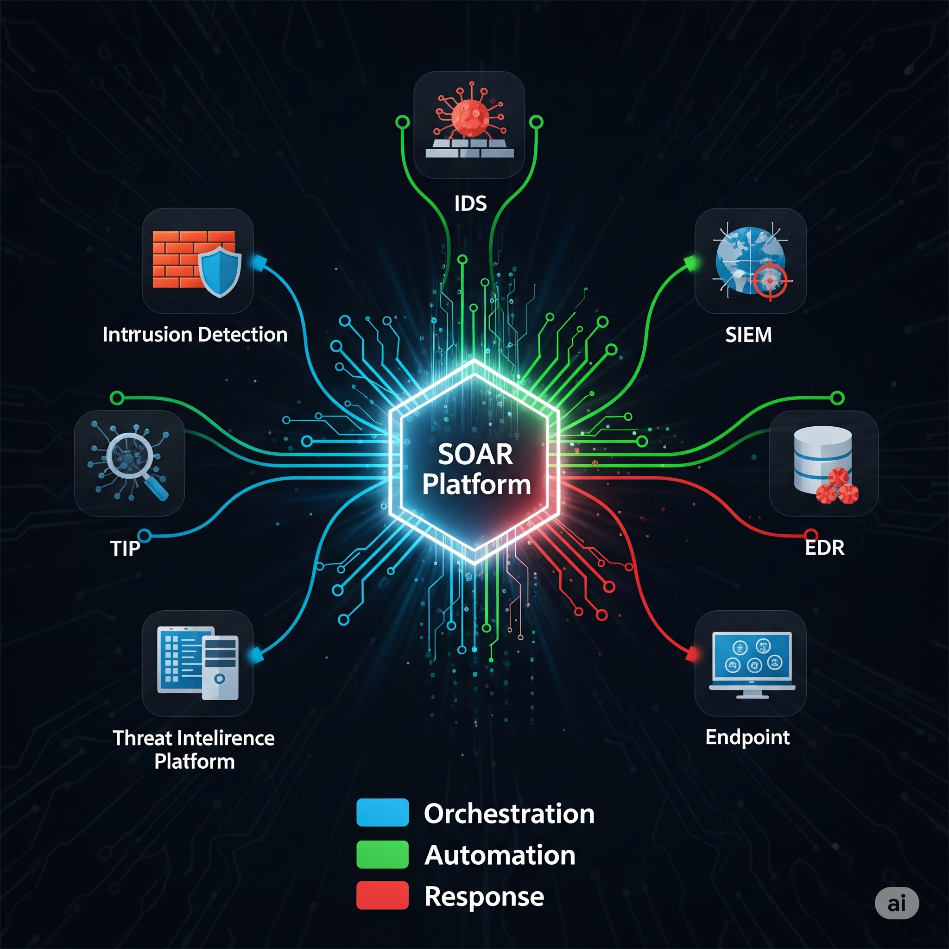
A SOAR platform is designed to revolutionize your security operations by:
Orchestration
Connecting and coordinating all your existing security tools – from SIEMs and EDRs to firewalls and threat intelligence platforms – into a unified, centralized system. This breaks down silos and ensures seamless data flow and communication across your entire security ecosystem.
Automation
Automating repetitive, mundane, and time-consuming tasks that typically bog down security analysts. Through pre-defined workflows known as "playbooks," SOAR can automatically enrich alerts with contextual data, block malicious IPs, quarantine infected endpoints, open incident tickets, and much more, at machine speed.
Response
Streamlining and accelerating incident response. By automating the initial stages of investigation and remediation, SOAR significantly reduces your Mean Time to Detect (MTTD) and Mean Time to Respond (MTTR). It enables consistent, rapid responses to threats, minimizing their potential impact.
Our SOAR service goes beyond just providing the technology. We offer a comprehensive service that includes:
Custom Playbook Development: Tailoring automated workflows to your specific security policies, threat landscape, and existing toolset.
Integration Expertise: Seamlessly integrating SOAR with your current security infrastructure and business applications.
24/7 Monitoring and Management: Our expert analysts continuously monitor and optimize your SOAR platform, ensuring it’s always performing at its peak.
Threat Intelligence Integration: Feeding the latest threat intelligence directly into your SOAR playbooks for proactive defense.
Training and Support: Empowering your security team to effectively leverage the SOAR platform for enhanced efficiency and effectiveness.
By implementing our SOAR service, your organization can overcome alert fatigue, free up analysts to focus on high-value threat hunting and strategic initiatives, and achieve a more proactive, resilient, and cost-effective cybersecurity posture. In the relentless battle against cyber threats, Security Operations Centers (SOCs) are often overwhelmed by a deluge of alerts, manual processes, and disparate security tools. This "alert fatigue" can lead to missed threats, delayed responses, and inefficient use of valuable analyst time. This is where a SOAR (Security Orchestration, Automation, and Response) service offered by UTCYBER becomes a game-changer.
A SOAR service is designed to revolutionize your security operations by providing a comprehensive approach that integrates the power of technology with expert human oversight. It encompasses:
Orchestration: Seamlessly connecting and coordinating all your existing security tools – from SIEMs and EDRs to firewalls and threat intelligence platforms – into a unified, centralized system. This breaks down silos and ensures seamless data flow and communication across your entire security ecosystem.
Automation: Automating repetitive, mundane, and time-consuming tasks that typically bog down security analysts. Through pre-defined workflows known as “playbooks,” our SOAR service can automatically enrich alerts with contextual data, block malicious IPs, quarantine infected endpoints, open incident tickets, and much more, at machine speed.
Response: Streamlining and accelerating incident response. By automating the initial stages of investigation and remediation, our SOAR service significantly reduces your Mean Time to Detect (MTTD) and Mean Time to Respond (MTTR). It enables consistent, rapid responses to threats, minimizing their potential impact.

Our SOAR service goes beyond just providing the technology. We offer a comprehensive, managed service that includes:
Custom Playbook Development
Tailoring automated workflows to your specific security policies, threat landscape, and existing toolset.
Integration Expertise
Seamlessly integrating the SOAR platform with your current security infrastructure and business applications.
24/7 Monitoring and Management
Our expert analysts continuously monitor and optimize your SOAR platform, ensuring it's always performing at its peak.
Threat Intelligence Integration
Feeding the latest threat intelligence directly into your SOAR playbooks for proactive defense.
Training and Support
Empowering your security team to effectively leverage the SOAR platform for enhanced efficiency and effectiveness
By implementing our SOAR service, your organization can overcome alert fatigue, free up analysts to focus on high-value threat hunting and strategic initiatives, and achieve a more proactive, resilient, and cost-effective cybersecurity posture.
Host Data Loss Prevention
Host DLP, also known as Endpoint DLP, focuses on monitoring and controlling data usage directly on individual devices. It goes beyond network-level protection by analyzing user actions, file transfers, application usage, and data movement on the endpoint itself. Our Host DLP service provides a comprehensive solution to:

Prevent Unauthorized Data Movement
Block or alert on attempts to transfer sensitive data via USB drives, cloud storage, email, instant messaging, print, or even screen captures, based on predefined policies
Enforce Data Handling Policies
Ensure that sensitive information, whether it's intellectual property, customer PII, or financial records, is handled according to your organization's compliance requirements (e.g., GDPR, HIPAA, PCI DSS).
Gain Granular Visibility
Provide detailed insights into how sensitive data is being accessed, used, and moved by employees, helping to identify risky behaviors and potential insider threats, both malicious and unintentional.
Mitigate Insider Risk
Proactively detect and prevent data exfiltration by employees, contractors, or third parties, significantly reducing the risk of data breaches.
By deploying our Host DLP service, organizations can extend their data protection perimeter directly to the endpoints where critical data is actively used, ensuring that sensitive information remains secure throughout its lifecycle, regardless of where your workforce operates.
