Why Canadian Businesses can't Afford to Ignore Cybersecurity Solutions in 2025 & How Managed IT Services Fill the Gap
- 15 April 2026
- Sayeed Shaikh
Every week brings a new headline: a hospital system encrypts patient data, a local government pays millions to a ransomware group, or a mid-sized company finds its trade secrets stolen. Now, Canada is included. According to the Canadian Centre for Cybersecurity, solutions in Canada, is one of the most desirable locations for cybercriminals in the G7. Even still, many Canadian companies, especially small and midsize companies, lack formal cyber defence programs.
The assumption that only large companies need cyber resources is naive. Smaller companies are more desirable targets due to their lower cyber defences. If your company is in the cloud, completely remote, or has a data footprint due to customer data, you have a significant risk.
Managed IT and cybersecurity tools have shown their usefulness. Canadian companies have the opportunity to employ the protection of an external cyber partner, one with the benefits and protection of an internal security operation, enough coverage, and no cost of a new internal security operation.

The cyber threat landscape in Canada has changed tremendously
Recent memory would see a simple firewall and an antivirus subscription as serviceable practices for cybersecurity for a lot of businesses. Those days have long passed. The world today varies extremely in relation to distant workforces, hybrid infrastructure in the cloud, third-party interfaces, and an abundance of connected systems, many of which provide plentiful opportunities for cyber attackers to breach a business.
Ransomware is a lot closer to a Threat Today than before
Ransomware security is an operational must now, with businesses in Canada’s entire nation and in every conceivable sector (industry), like healthcare, education, financial services, and logistics, having all found themselves targets of ransomware security. Groups today implement a practice of exfiltrating and encrypting data and even threaten to publish the data if the initial payment for the ransom is not paid. There is no such thing as an impenetrable backup today, and the legal and social reputational harm an organization would face from loss is significant.
The resources for such an attack go further than simple reactive mechanisms. The systems and services for such an attack are both difficult to create and sustain without significant resources, so when considering the operational costs for such a service, it would make the direct costs for the service negligible.
Cloud Migration And Attack Surfaces
While the cloud has helped Canadian businesses significantly increase efficiency, there is a downside. More complex and broadened surfaces for attack have developed. Current-day cloud attacks usually exploit misconfigured cloud storage, too-flexible Identity and Access Management (IAM) systems, and exposed Application Programming Interfaces (APIs). With the correct scope, security for the cloud goes further than a cloud-native firewall. It involves visibility and presence, which are continuous throughout multi-cloud and hybrid systems, along with policy deployment and automated, proactive, and responsive cloud security posture management (CSPM). These capabilities should be readily adaptable to your needs as the cloud expands.
Insider Threats And Identity Risks
While the major threats to a business are usually external, there are several effective attacks the attacker can accomplish from the inside. Attacks involving identity typically come from credential manipulation, accidental leakage, and insider threats. Zero-trust implementation is a best practice. Zero-trust requires that all users from all locations of the organization, with all devices and all cloud services, be neither inherently trusted nor untrusted. Once zero-trust is implemented, identity management, multi-factor credential systems, and removal of trusted pathways to privileged services become necessary. These are sophisticated designs, and untrained IT personnel typically lack the necessary skills.

The gap between Managed IT Services and Managed SOC enhanced their services to secure their customers further
The Managed Security Services Model for Secure Protected Environments
Most small and medium-sized Canadian businesses are often caught in a pressure system, whereby they are expected to provide in-house costly services to handle alerts. Managed SOC services enable businesses to use the security operations centre as a service. Because of this, the Managed Service Model has enabled enterprises to shift their expenditures and economically manage their security based on their business needs.
The Managed SOC Services Capabilities
Fully managed SOC services extend beyond traditional bounded perimeter and endpoint protection systems. Managed SOC services include:
– Managed Detection and Response: 24/7 endpoint and network protection services and cloud workload protection to enable validated alerts and response services.
– SIEM as a Service: Integrated collection, routing, and analysis of security services complemented with workload-based machine learning anomaly and correlation detection.
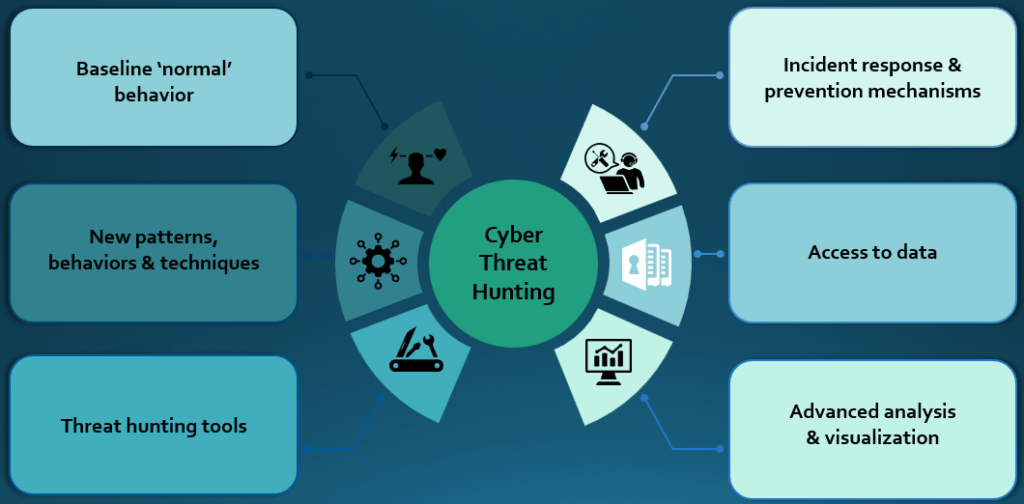
– Personnel-supported hunting services.
– Managed Endpoint Protection: 365 analysis for protection and limited services.
– Managed Resolution Services: Tailor-made stratified handling of incidents with documented and seamless post-action communication.
– Breach Prevention Services: Advanced grunt-based protection and novel service provision.
The Philosophy That Matters, Security Without Borders
Additionally, the most pertinent shift in cybersecurity is the dismantlement of perimeter-centred security. Under the philosophy of ‘Security Without Borders,’ the protection of users and data becomes paramount, irrespective of the location of the data, be it in the cloud, a personal device, or the data of a partner organization. Integrated security must be affordable across all environments, embracing consolidated, perpetual, cross-the-board security.
Cloud Services & Consulting: Forge the Future and Security
Many organizations look at cloud consulting to create cost efficiencies through faster and cheaper deployment and scalable infrastructure. However, cloud migration entails a security shift. Cloud security consultants partner with organizations to help develop a security framework that is integrated at the outset during the design and build of the cloud environment and is not merely documented for compliance. This includes various cloud types (private and hybrid), improving resilient security across cloud Kubernetes services, safe and economical cloud cost management, and DRaaS that ensures the resiliency of the organization post a significant disruption.
Managing Compliance (From ISO 27001 to PIPEDA and More)
In Canada, risk management and security cannot be evaluated in isolation. Compliance with a growing list of laws and regulations is required. With the data you manage and the industry in which you operate, you will likely go through a variety of compliance frameworks, including PIPEDA, applicable provincial privacy laws, HIPAA (in case you manage US healthcare data), PCI DSS (in case you manage data relating to payment cards), SOC 2, and the General Data Protection Regulation (GDPR) relating to the protection of EU persons, not to mention multiple specific industry frameworks and operating under the Sarbanes-Oxley Act (SOX).
Much more than a simple policy is needed to satisfy these expectations. Written evidence of continuous control is becoming a necessity for auditors and regulators. This includes logs of control, access, and review, as well as documentation of vulnerability scans, control incidents, and responses. Maintaining these records can consume considerable resources. Automating this process is easier and more efficient from a managed security platform.
Investing in compliance is better than having a checklist complied with to satisfy an auditor. Taking compliance structures seriously, in the Digital Security and Privacy Framework and Controls (NIST CSF) and the International Organization for Standardization (ISO 27001), develops an organization’s security.
Desktop as a Service (DaaS) and Virtual Desktop Infrastructure (VDI) are the other inclusions for Digital Security in the pandemic and beyond.
The move to remote and hybrid working has presented businesses with different security and privacy challenges. Remote control has eliminated traditional protected endpoint devices, leading to serious workforce security challenges. There is now a potential for control, security, and compliance vulnerability as devices are compromised to ensure control and compliance security. DaaS and VDI enable the organization to keep sensitive information in a protected location by maintaining control and compliance over remote workforce security on compromised, unprotected devices.
The technologies offer a compelling value proposition of simultaneously improving productivity and security by reducing the effort needed to ensure security (through the automation of security compliance) for organizations with a distributed remote workforce, either across downtown, across Canada, or Globally.
Choosing Your Cybersecurity Partner in Canada
How do you choose the right Managed Security Services Provider (MSSP) in the ever-growing field of cybersecurity? The right Canadian MSSPs for your firm would have the following attributes:
– Experience – They would have hands-on experience in the industry. They would have the skills necessary due to the many years designing architecture, responding to incidents, or deploying valuable security tool sets.
– Technology Alignment – If your firm has a hybrid environment of M365 and Azure, a Canadian MSSP firm would need a deep specialization with the Microsoft and Azure security stack, including Microsoft Defender, Entra, and Azure Sentinel.
– Flexible, Agile Services – Many Canadian MSSPs can complement your services, whether your firm requires a fully managed Security Operations Centre (SOC) or a co-managed service.
– Knowledge of Regulations – In building a program to address the needs of your firm and the auditors, the firm should help decrease its risk and address the needs of the auditors.
– Monitoring and Threat Intelligence – For your firm to consistently rise in a leading manner, the firm must be proactive. Monitoring services help mitigate your firm’s risk.
– Rapid, Effective Response – If the firm experiences a security breach, it would have the plans and good communication skills necessary to control and contain it. They would have the qualifications to perform the necessary technical repairs.
The Bottom Line: Security Is an Enabler, Not Just a Cost Centre
Most people think of cybersecurity as a black hole for resources. With mature security, the opposite is actually true. Companies have fewer disruptions, quicker and more thorough scans for customer satisfaction, company recovery, and the satisfaction of deep client and partner trust and loyalty, all leading to positive business growth.
For Canadian businesses that are trying to keep up with the ever-growing and changing threat landscape, the question is how to spend your resources on defence with the greatest potential upside, rather than if you will spend your resources. One proven example of defence with the least resources and the highest positive upside is CTL, Canadian Technology Limited. A top Canadian IT and PT managed services company. This is also true because CTL has an upper and lower as well as the true potential of your natural resources.
Your digital ecosystem is expanding. Your attack surface is growing with it. The right security partner doesn’t just protect what you’ve built; they protect your ability to keep building. That’s business continuity, competitive advantage, and peace of mind, all in one.




