Enterprise Cloud Security in Canada: A complete Guide to Protecting Your Multi-Cloud Environment in 2025
- 15 Jan 2026
- Sayeed Shaikh
In 2025, the cloud will be the Canadian business ecosystem in which companies collaborate and safely store all of their assets. It will be the battleground of Canadian companies’ most important and hardest-lost cyber battles. The most common cause of Canadian business data breaches will be cloud misconfigurations. Relying on social engineering and other persuasion techniques will. Replacing malware will become the most common hacking technique. The average business will have a complex attack surface of on-premises private cloud, Azure, and AWS. Because of this, traditional security tools will become obsolete. This will become the main issue for enterprise cloud security.
What will set businesses apart from the average Canadian company will not be the security budget; it will be the most comprehensive business security. Organizations will be going beyond a tool-defence-focused system and investing in a security system that allows for the unprecedented level of continuous scanning and responding to threats in real-time and provides preventive threat defence across their cloud infrastructure.
What real enterprise cloud security looks like is described in this guide and will provide a comprehensive explanation of enterprise cloud security for Canadian companies to know what to expect from their security vendors.
Why Enterprise Cloud Security Is Fundamentally Different From Traditional IT Security
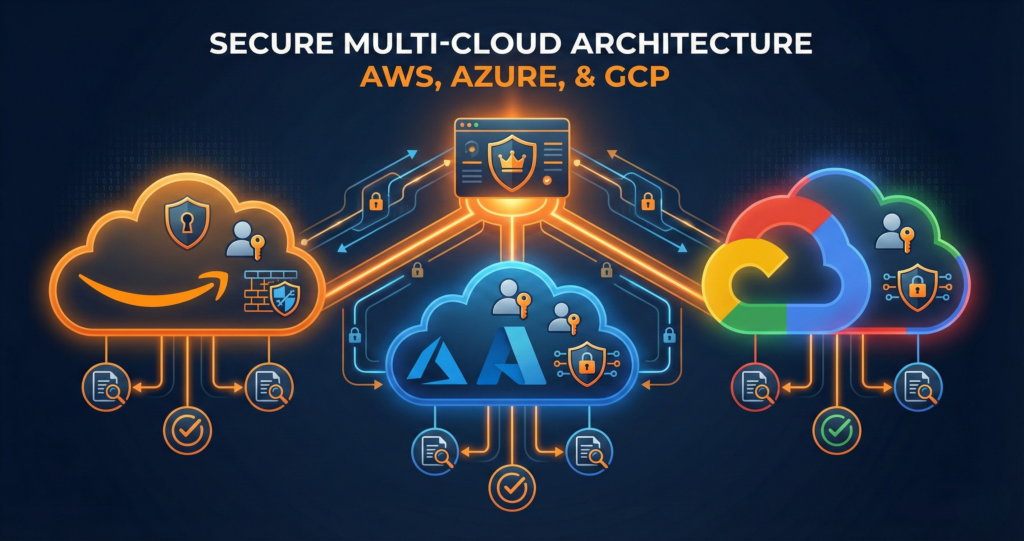
Establishing security for a classic on-premises environment is a challenge. Ensuring security for enterprise cloud environments is more challenging. This includes hybrid and multi-cloud environments, which straddle private infrastructure, Azure, and AWS. Such complexity is structural and not superficial.
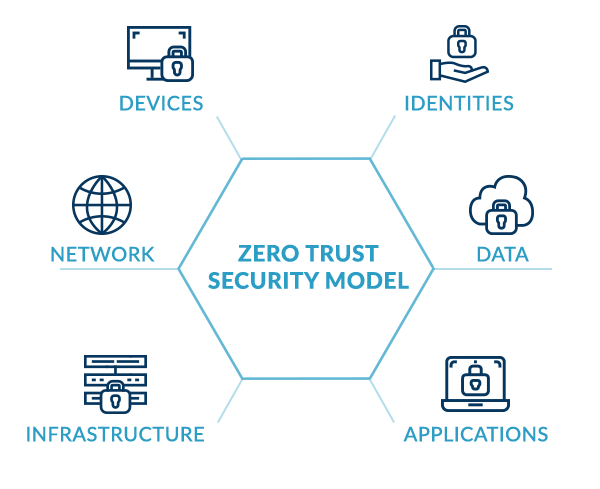
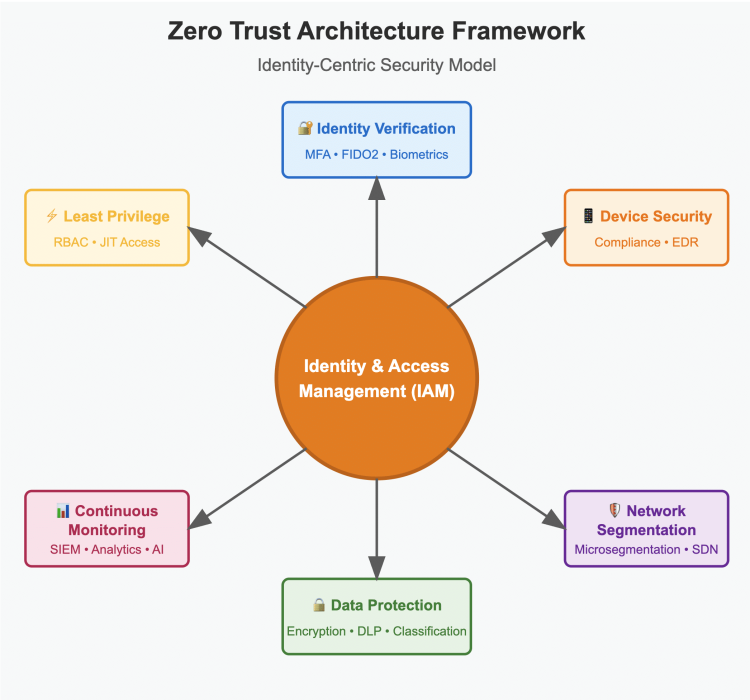
There is a visible perimeter, which is largely static in a traditional environment. There is a defined boundary, which is protected by firewalls and network segmentation. In a cloud environment, that boundary is eliminated entirely. Different applications communicate with one another via APIs. Users can authenticate from anywhere and at any time, regardless of the device. Data can and does flow continuously from one system and service to another. These include various cloud services, SaaS applications, and on-premises systems. Identities replace IP addresses in becoming the new perimeter.
AWS alone has more than 200 services, and they all come with their own security configuration. Configuring said services, particularly S3 buckets, IAM policies, and security groups, can expose data to the public, which has happened before. Microsoft Azure is similar in nature. Operating a hybrid environment is a great and risky challenge, and an enterprise cloud security tool that is purpose-built is needed. This is in conjunction with private cloud, on-prem Google, and Microsoft systems. Attackers make configuration errors, which attackers rely on virtually inevitably.
The Seven Pillars of UTCYBER's Enterprise Cloud Security Platform
UTCYBER’s approach to enterprise cloud security is built around seven integrated service pillars that collectively address every layer of the modern cloud threat landscape. Together, they deliver the depth of coverage that Canadian enterprises need to operate confidently in complex cloud environments.
Security Domain | Key Capabilities | Value Delivered |
Security Consulting | Network security, endpoint EDR, data security, application security, IAM, cloud security, compliance & governance | Strategic roadmap aligns defences to business risk; eliminates security silos across all infrastructure layers |
Cybersecurity Assessment | Vulnerability assessment, penetration testing, security audits, risk assessment, social engineering, architecture review | Uncovers real exploitable gaps before attackers find them; provides prioritized, actionable remediation roadmap |
Azure Sentinel Consulting | Centralized log ingestion, threat intelligence integration, KQL threat hunting, SOAR playbooks, AI-powered UEBA, compliance reporting | Maximizes ROI on Microsoft Sentinel; reduces MTTR through automation; delivers cloud-scale SOC visibility |
Hybrid Multicloud Security | Unified IAM across Azure AD and AWS IAM, centralized SIEM, data protection (Azure Key Vault, AWS KMS), IaC automation (Terraform, Ansible) | Eliminates fragmented security across private cloud, Azure, and AWS; consistent policy enforcement everywhere |
Public Cloud Security | Azure: Defender for Cloud, Azure Firewall, NSGs, WAF, DDoS Protection. AWS: GuardDuty, Security Hub, WAF, Shield, VPC, CloudTrail | Native cloud security maximized; continuous compliance against ISO 27001, HIPAA, PCI DSS, GDPR |
Audit and Reporting | Regulatory compliance verification (GDPR, HIPAA, PCI DSS, SOX, ISO 27001), risk reporting, continuous monitoring feedback loop | Audit-ready evidence for regulators and insurers; informed board-level decision-making; continuous improvement cycle |
Dark Web Monitoring | Compromised credential detection, threat actor TTP intelligence, real-time alerts, continuous scanning of dark web marketplaces and forums | Early breach warning before attackers act on stolen data; protects brand reputation and customer trust |
Security Consulting and Cybersecurity Assessments: Building the Right Foundation
The beginning of every enterprise cloud security program is the current situation’s clear and honest evaluation. Without the current situation assessment, security expenditures rely on the vendor links and purchasing simplicity rather than the actual risks. The unaddressed gaps are the ones attackers will exploit.
The Areas that Need to be Covered in a Full Cybersecurity Assessment
Cybersecurity consulting from UTCYBER has developed several assessment methods, each identifying a distinct type of risk. These methods are:
– Vulnerability Assessment – Automated and manual network, application, and endpoint assessments to identify missing patches, errors, and known vulnerabilities and help your organization illuminate the baseline of its exposure.
– Penetration Testing – Attacks that simulate potential breaches in your external perimeter, internal network, and both web and mobile applications. Unlike vulnerability scanning, penetration testing clarifies the exploitable vulnerabilities and what an attacker is capable of once the perimeter has been compromised.
– Security Architecture Review – Evaluation of your cloud, network, and system architecture to identify and mitigate lateral movement, privilege escalation, and data exfiltration.
– Social Engineering Assessment – Phishing, dumpster diving, and other hybrid pretexting to identify weaknesses in the human element. The human actor has become the most exploitable attack vector of your organization.
– Risk Assessment – A ranked remediation roadmap that identifies the right security investment by determining the vulnerabilities that need to be addressed and the exposures that need to be prioritized.
These assessments shouldn’t be a report that’s filed away. Instead, they should create a practical and sustainable pathway that outlines how to achieve a security posture that is genuinely resilient, proportionate to actual risk, and demonstrably compliant with the regulators.
Azure Sentinel Consulting: Maximizing Your Cloud-Native SIEM Investment
Microsoft Azure Sentinel has emerged as one of the most powerful cloud-native SIEM and SOAR platforms available to Canadian organizations — particularly those already operating within the Microsoft ecosystem. But Sentinel’s power is directly proportional to how well it is configured, and most organizations deploying it independently fail to capture even a fraction of its potential. This is where Azure Sentinel consulting from UTCYBER delivers disproportionate value.
UTCYBER’s Sentinel consulting practice covers the full implementation lifecycle:
- Centralized log ingestion architecture — designing the connector strategy that pulls security data from Microsoft 365, Azure services, on-premises infrastructure, AWS workloads, and third-party security solutions into a single, unified visibility plane.
- Custom detection rule development — building and tuning detection rules using Kusto Query Language (KQL) that are specific to your environment, your threat model, and the adversary TTPs most relevant to your industry.
- SOAR playbook implementation — automating incident enrichment, containment, and escalation workflows so that Mean Time to Respond (MTTR) drops from hours to minutes. When a compromised account is detected, an automated playbook can disable the account, alert the security team, and begin evidence collection — all before a human analyst has opened the alert.
- AI-powered UEBA configuration — activating and tuning User and Entity Behaviour Analytics to detect subtle insider threats and compromised account activity that signature-based rules cannot identify.
- Compliance dashboard build-out — configuring Sentinel’s reporting and dashboarding capabilities to produce the continuous compliance evidence required for PIPEDA, ISO 27001, HIPAA, and PCI DSS audits.
A properly implemented Azure Sentinel environment transforms your security operations from a reactive, tool-by-tool posture into a unified intelligence platform that sees across your entire environment and responds in seconds.
Hybrid Multicloud Security: Consistent Protection Across Private Cloud, Azure, and AWS
The majority of Canadian enterprises today operate in hybrid or multi-cloud environments — a combination of on-premises infrastructure, private cloud, and at least two major public cloud platforms. This architectural reality creates the central challenge of hybrid multicloud security: how do you enforce consistent security policies, maintain unified visibility, and demonstrate compliance across environments that were built by different vendors, using different native tools, with different IAM models and different network constructs?
The answer is not to pick one platform’s security tools and force them to cover the others. It is to build a security architecture that aggregates and normalizes data from all platforms, enforces consistent identity and access controls through federated IAM, and automates security operations through Infrastructure as Code so that configurations remain consistent and drift is detected automatically.
Security Domain | Azure Capability | AWS Capability |
Identity & Access | Azure AD, MFA, Conditional Access, RBAC, PIM | IAM roles/policies, AWS SSO, Amazon Cognito, MFA enforcement |
Threat Detection | Microsoft Defender for Cloud, Azure Sentinel (SIEM) | Amazon GuardDuty, AWS Security Hub, AWS Detective |
Data Protection | Azure Key Vault, Storage Service Encryption, DLP | AWS KMS, S3 encryption, Amazon Macie (sensitive data discovery) |
Network Security | Azure Firewall, NSGs, DDoS Protection, WAF | AWS VPC, Security Groups, Network ACLs, WAF, AWS Shield |
Audit & Compliance | Azure Policy, Compliance Manager, Azure Monitor | AWS Config, AWS Audit Manager, CloudTrail API auditing |
Automation & IaC | ARM Templates, Bicep, Azure DevOps pipelines | AWS CloudFormation, Terraform, AWS CodePipeline |
UTCYBER’s hybrid multicloud security practice designs and implements exactly this architecture — unifying Azure Monitor, AWS Security Hub, and your private cloud’s telemetry into Azure Sentinel for a single pane of glass, while harmonizing IAM policies across Azure Active Directory and AWS IAM to enforce least-privilege access consistently. Terraform and Ansible automate security configuration deployment, ensuring that security controls are applied consistently at scale and that any configuration drift triggers an immediate alert.
Dark Web Monitoring: The Early Warning Layer Most Businesses Overlook
The purpose of most layers of enterprise cloud security is to stop attackers from getting inside. Dark web monitoring solves another crucial layer of cloud security. What if your employee’s credentials are already being sold? What is the security risk of your employee’s credentials being exposed?
Every data breach leads to the dark web. Breaches lead to exposed credentials to email accounts, emails, accounts, accounts with money, and accounts with personal information. There are so many accounts, and they all get leaked to the dark web. Dark web monitoring is particularly important for Canadian businesses. Canadian businesses typically do not have access to dark web intelligence, monitoring, and control to see that an employee’s corporate account credentials have been exposed by some third service, and those credentials can be purchased to be used to break-in to systems and cloud accounts.
The UTCYBER dark web monitoring service keeps track of underground markets, paste sites, chat rooms, and forums. This service looks for your corporate emails, credentials, financial data, information, and intellectual property. When the dark web finds something, they send out the credentials to cloud accounts. When people, especially employees, are exposed on the dark web, UTCYBER’s monitoring service is the first to alert your corporation. These employees and their cloud access will lead to an incident. The monitoring service of UTCYBER will describe why the employees were exposed and will describe why the cloud accounts will lead to an incident. The monitoring service will, at the very least, rapidly enforce a controlled cloud breach by resetting cloud access credentials and suspending access.
Dark web monitoring is a beneficial feature of PIPEDA’s breach notification requirements for Canadian businesses. The early detection ability of dark web monitoring decreases the time it takes for a breach to happen and for an organization to become aware of it. This allows your organization to work within its control before the situation becomes a breach and necessitates notification.
Audit, Reporting, and Compliance: Turning Security Into Demonstrable Evidence
Think of security without evidence as wishful thinking. Nothing short of substantial proof of security controls will satisfy cyber insurers, regulators, enterprise customers subjected to vendor assessments, or boards of directors. For UTCYBER, the solution to substantiating security controls is found in the audit and reporting services provided by UTCYBER.
The compliance component of UTCYBER’s services is comprehensive and includes all Canadian enterprise security frameworks and data privacy legislation, PIPEDA and the various provincial privacy laws, the General Data Protection Regulation (GDPR) for clients with data in Europe, the Health Insurance Portability and Accountability Act (HIPAA) for health-related enterprises, the Payment Card Industry Data Security Standard (PCI DSS) for enterprises dealing with payment cards, the Sarbanes-Oxley Act (SOX) for publicly traded companies, and the International Organization for Standardization (ISO) 27001 established for enterprises seeking internationally accepted security standards. With each of these frameworks, UTCYBER’s staff evaluates the client’s existing controls, identifies the missing security controls, and provides the evidence to be submitted to auditors and/or regulators. UTCYBER provides continuous compliance discipline to clients by way of constant security controls, in-house enterprise cloud security, and the flexible UTCYBER Compliance Framework. With UTCYBER’s services, compliance is non-negotiable.

The Integrated Security Posture Your Cloud Environment Actually Requires
The age of using individual point-solution cybersecurity tools for endpoints, networks, clouds, etc., that don’t integrate with one another, is completely over for any organization that genuinely cares about its security. The threats of today’s world have become immensely more challenging and more sophisticated, so the only way to combat them is through a sophisticated and fully integrated solution.
UTCYBER’s enterprise cloud security platform provides that integration with real consultancy and penetration testing to really find and fix vulnerabilities, Azure Sentinel to provide a cloud SOC with AI detection and SOAR automation, hybrid multicloud security to provide cross cloud security and policy control for private cloud, Azure, and AWS, and dark web monitoring to prevent the taking over of accounts with lost credentials, along with audits and reports on security defenses that have been put in place and spendings to provide justified security (regulatory) due diligence.
This level of integration for enterprise security cloud services will be a baseline requirement for 2025, and the trading environments for Canadian businesses, from a security standpoint, have never been more difficult, or of greater consequence.
Your cloud systems give your business a competitive edge. Protecting them with the advanced methods you used to develop them isn’t just a cybersecurity decision, it’s a business decision. UTCYBER’s enterprise cloud security services will help Canadian companies protect the security of the cloud systems they have used to develop a competitive edge while also making the security of the cloud more of a reality and considerably less difficult.




